Picture: Kitra Cahana/The New York Times
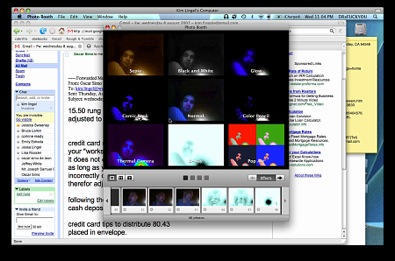
I’ve confirmed that the iPhone no longer runs software applications as “root” — but the iPhone is still insecure, a security expert says.
As reported on Wired.com, the iPhone used to run all software applications as “root” until recently, a flawed architecture that could give hackers complete control of the device. If hackers found a hole in any application, they could take over other functions, using the iPhone to make calls, take pictures or read and send email.
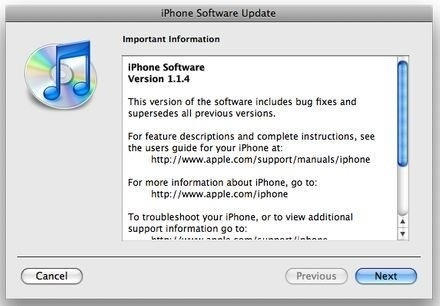
But last month Apple released a firmware update, version 1.1.3, that put most of the major applications in a new account called “mobile.”
While this is better than running all applications in root, it still lumps the applications together, which doesn’t much improve things: The same vulnerability still exits. If any one application is compromised, they are all vulnerable — and the iPhone can still be taken over, says Charlie Miller, principal analyst of software security at Independent Security Evaluators.
Dr. Miller was one of the first security experts to document the iPhone’s flawed architecture.
In a response to an email query sent yesterday, Dr. Miller writes:
Actually, the important apps have not been running as root at least since 1.1.3. See below. This is obviously better than running everything as root.
However, now they seem to run everything unimportant as the user “mobile”.
This doesn’t really solve their security problems because, for example, someone gaining access through a web server attack will still be able to access emails, dial the phone, etc. (At least it appears this way, I haven’t verified this).
A better approach would have been one like the folks at Google took with their Android SDK.
There, every application runs as a separate user in their own directory.
Therefore, each application cannot access the data of another application without the system having explicitly been told to allow it.
In the above example, an attacker who gains access to an Android phone through the web browser could only access things the web browser deals with, such as bookmarks.
They would not have access to mail contacts, saved messages, SMS messages, etc. (at least without doing a second type of attack).
Hope that helps.
Charlie
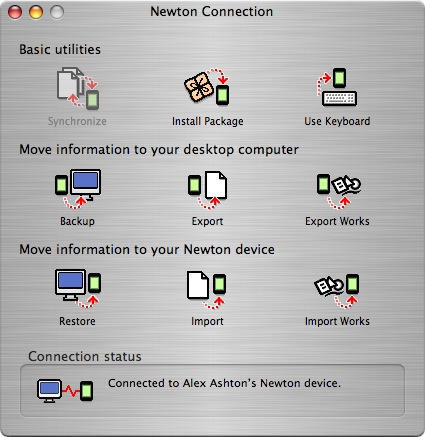
# uname -a
Darwin Charlie Miller’s iPhone 9.0.0d1 Darwin Kernel Version 9.0.0d1: Wed Dec 12 00:16:00 PST 2007; root:xnu-933.0.0.211.obj~2/RELEASE_ARM_S5L8900XRB iPhone1,1 unknown # ps aux
USER PID %CPU %MEM VSZ RSS TT STAT STARTED TIME COMMAND
mobile 62 2.8 20.3 325440 24080 ?? Ss 9:36AM 1:15.31 /System/Library/CoreServices/SpringBoard.app/SpringBoard
root 1 0.0 0.4 272956 444 ?? Ss 8:56AM 0:01.06 /sbin/launchd
mobile 12 0.0 1.4 286128 1604 ?? Ss 8:56AM 0:00.37 /usr/sbin/BTServer
root 13 0.0 1.3 282168 1556 ?? Ss 8:56AM 0:03.43 /System/Library/Frameworks/CoreTelephony.framework/Support/CommCenter
root 16 0.0 1.3 275864 1516 ?? Ss 8:56AM 0:15.53 /usr/sbin/configd
root 17 0.0 0.5 273404 592 ?? Ss 8:56AM 0:00.09 /usr/libexec/crashreporterd
mobile 18 0.0 1.4 284764 1632 ?? Ss 8:56AM 0:00.86 /System/Library/Frameworks/IAP.framework/Support/iapd
root 19 0.0 0.7 273732 880 ?? Ss 8:56AM 0:01.69 /usr/sbin/mDNSResponder -launchd
root 20 0.0 1.1 284208 1296 ?? Ss 8:56AM 0:01.25 /usr/libexec/lockdownd
root 21 0.0 0.4 274000 432 ?? Ss 8:56AM 0:07.57 /usr/sbin/syslogd
root 22 0.0 0.2 264644 276 ?? Ss 8:56AM 0:00.66 /usr/sbin/update
mobile 23 0.0 0.7 273576 792 ?? Ss 8:56AM 0:00.12 /usr/libexec/ptpd -t usb
mobile 24 0.0 1.7 290148 2072 ?? Ss 8:56AM 0:03.31 /usr/sbin/mediaserverd
root 26 0.0 0.4 273456 428 ?? Ss 8:56AM 0:01.14 /usr/sbin/notifyd
mobile 64 0.0 2.0 309600 2340 ?? S 9:36AM 0:00.93 /Applications/MobilePhone.app/MobilePhone –launchedFromSB –firstLaunch —
mobile 65 0.0 2.5 309112 2940 ?? S 9:36AM 0:02.78 /Applications/MobileMail.app/MobileMail –launchedFromSB –firstLaunch –su
root 81 0.0 7.8 315532 9324 ?? S 9:43AM 0:37.71 /Applications/Installer.app/Installer –launchedFromSB
mobile 82 0.0 12.7 321948 15036 ?? S 9:45AM 0:21.86 /Applications/MobileSafari.app/MobileSafari –launchedFromSB
root 97 0.0 0.6 273276 764 ?? S 9:54AM 0:00.81 /usr/sbin/sshd -i
root 98 0.0 1.0 274168 1164 p0 Ss 9:54AM 0:00.14 -sh
root 100 0.0 0.3 272876 332 p0 R+ 9:54AM 0:00.01 ps aux
Why was the iPhone architected like this, I asked Dr. Miller? His reply: “I think they did it that way because it was the easiest and quickest way to do it. They had a deadline, they had a great product and they wanted to get it out the door and start making money. Clearly, by not running things as root, they are going back and trying to make the things more secure now that the phones are out and in use. However, adding security after the fact if much more difficult (and expensive) then designing it in from the start.”