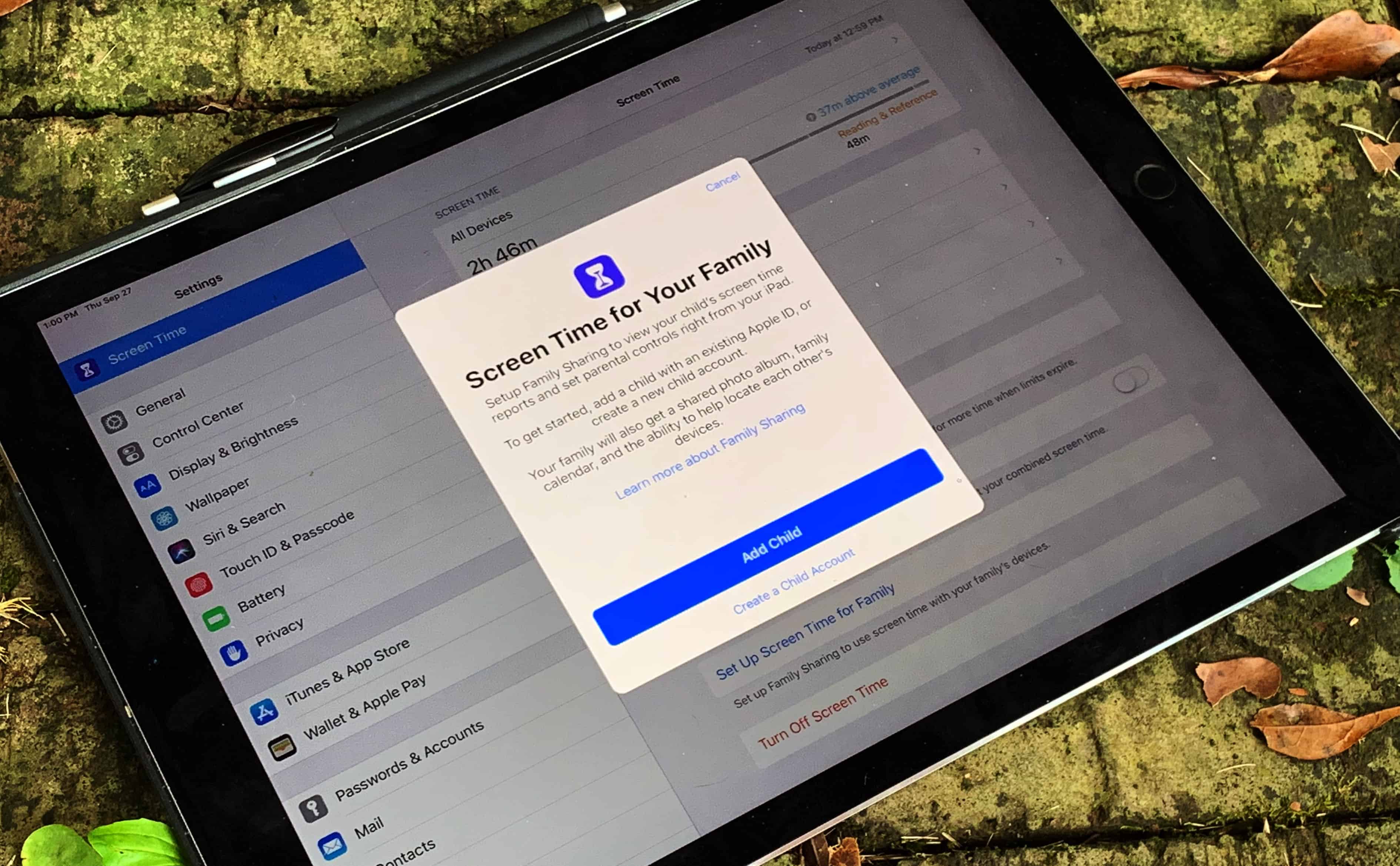
Wouldn’t you love to have half a dozen M-series MacBooks in your computer setup? One second thought, maybe that’s too much of a good thing. And it might only come up if you had to use most of them for work, like in today’s featured setup. A mobile device management (MDM) engineer does a lot of MDM testing on MacBooks for his job. If you use a Mac for work, he’s the guy who makes sure it keeps working efficiently and securely.
Software engineer shows off parade of powerful MacBooks [Setups]
![Software engineer shows off parade of powerful MacBooks [Setups] MDM testing on MacBooks](https://www.cultofmac.com/wp-content/uploads/2025/01/Setups-ajpinton-Reddit-Jan-15.-2025.jpeg)
Photo: [email protected]







![Three Critical Business Dilemmas The iPhone 5 Will Create [Feature] Even before its launch, the iPhone 5 is creating concerns and challenges for businesses and IT departments.](https://www.cultofmac.com/wp-content/uploads/2012/09/7378963508_e8a458a51b_z-1.jpg)
![How To Deploy iOS 6 In Business The Right Way [Feature] iOS 6 has lots of business potential, but having a plan about rolling it out is critical.](https://www.cultofmac.com/wp-content/uploads/2012/08/ios6-business.jpg)
![What IT Wants To See In iOS 6 [Feature] iOS 6 will deliver a lot of business features, but what about enterprise/IT integration?](https://www.cultofmac.com/wp-content/uploads/2012/08/ios6-120611.jpg)





![Why Apps (Not MDM) Are The Future Of iPhone Management [Feature] Mobile management means securing apps and content as well as locking down devices.](https://www.cultofmac.com/wp-content/uploads/2012/08/confusion-mam.jpg)