A Bluetooth LE security flaw could let malicious actors discover people’s iPhone numbers using Apple’s file-sharing AirDrop feature.
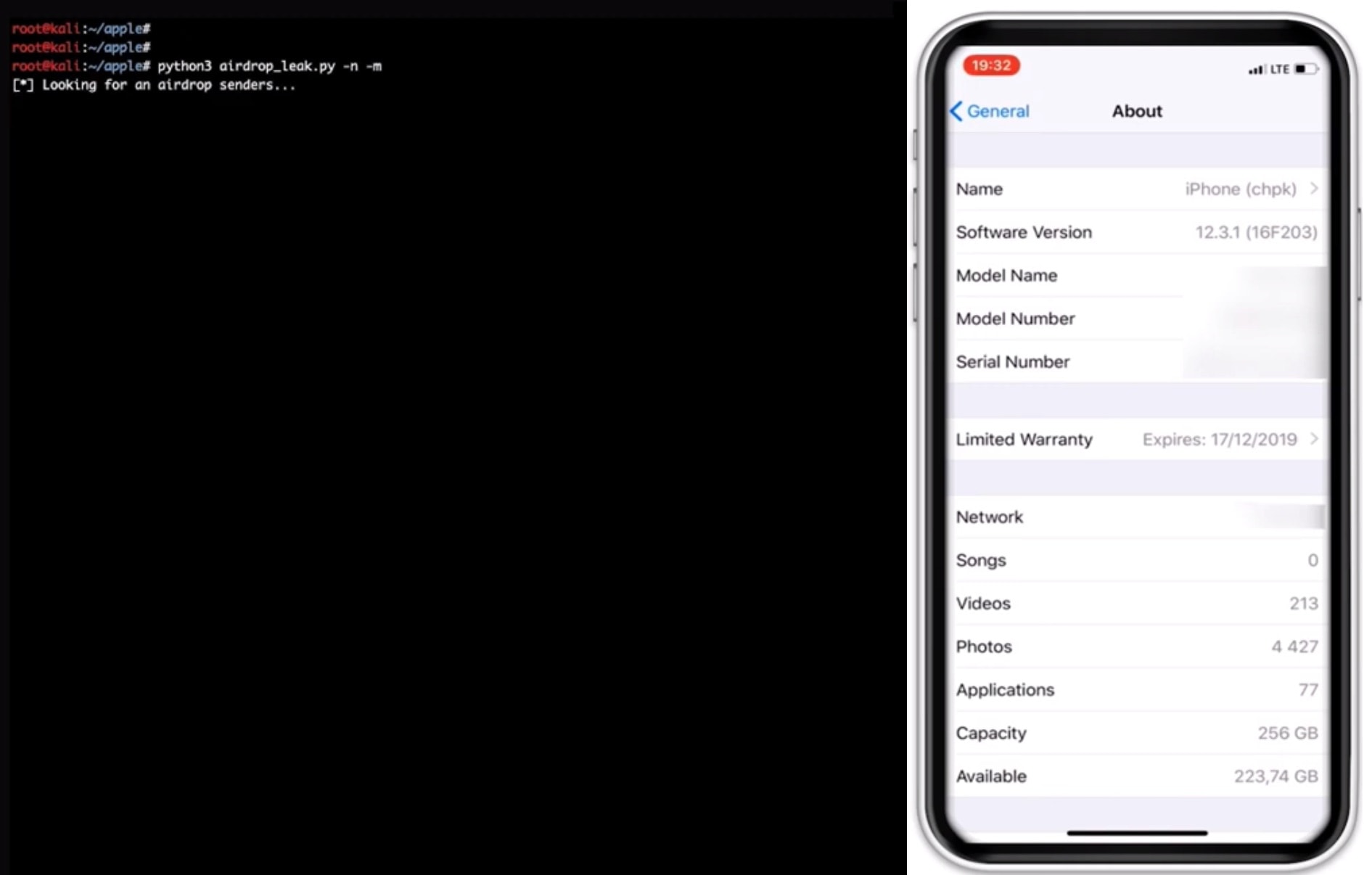
An attacker would need to create a phone number database for a specific region. Using a special script, they then could collect information on users who tried to AirDrop a file.
As ArsTechnica notes:
“Simply having Bluetooth turned on broadcasts a host of device details, including its name, whether it’s in use, if Wi-Fi is turned on, the OS version it’s running, and information about the battery. More concerning: using AirDrop or Wi-Fi password sharing broadcasts a partial cryptographic hash that can easily be converted into an iPhone’s complete phone number. The information—which in the case of a Mac also includes a static MAC address that can be used as a unique identifier—is sent in Bluetooth Low Energy packets.”
The flaw stems from the fact that using Apple’s AirDrop feature broadcasts a partial SHA256 hash of the user’s phone number. In the event that Wi-Fi password sharing is on, the flaw lets hackers pick up phone numbers, email addresses and Apple ID information.
The devices only send the first three bytes of the hash. However, researchers for security firm Hexway showed that it’s possible to recover a complete phone number.
Errata Security CEO Rob Graham installed the proof-of-concept tool on his laptop. Within a couple of minutes, Graham captured details of more than 12 iPhones and Apple Watches in the area.
Security issues
Apple, long renowned for its security, hasn’t had the best time as of late. Recently, members of Google’s Project Zero team discovered some security flaws in Messages. Apple published an iOS 12 update to patch the vulnerabilities.
Unfortunately, this latest vulnerability is another illustration of how ease of use can conflict with security. While some technologies (Face ID, for instance) can do both, in other cases there’s a more serious trade-off.