Replacing UDID With A SDK
Velti works with 35 ad networks and over 18,000 publishers to deliver targeted ads for mobile. The company essentially gives a SDK for publishers to insert into their apps that hook into ad networks. Since Apple announced the deprecation of UDIDs, Velti has been trying to form a working group to address concerns and find a new solution.
“From an education standpoint, one of the most important things is making sure consumers understand that targeting is important. We want to be able to connect users to ads and content they are interested in,” Velti told Cult of Mac.
According to Velti, nearly two thirds of all iOS apps rely on the UDID for either ads or services. If a new solution isn’t implemented, “It would very realistic for a consumer to pick up a phone and have 10 different apps that display the same ad every day of the week,” said Velti. “There would be no way for advertisers to identify a unique user action. That’s what the industry is trying to make sure doesn’t happen.”
Velti is pushing a solution called Open Device Identification Number (ODIN) for its publishing partners to implement. ODIN creates a device ID with its MAC address and adds a one-way hash so the identifier cannot be reversed and tied to a specific device. Implementing the MAC address introduces some problems.
MAC Address Is No Good
The only other hardcoded piece of data that identifies an iPhone is the MAC address. It’s been around in computing for decades. It’s how networking works at the basic level. According to some developers, there have been whispers that the UDID is even derived in part from the MAC address. Using the MAC address in any way — even hashed — as a UDID replacement is a terrible idea, though, because it is still an irreversible, single identifier… and therefore has the same privacy issues as UDID.
“At this point the only 100% safe solution is to just not send out the UDID/MAC addresses in any form,” Paul Haddad of Tapbots told Cult of Mac. What’s to keep Apple from banning use of the MAC address if the same privacy infringement concerns arise in a few months?
Other Feeble Attempts
There are several different ways companies are trying to replace the UDID, but many of them are flawed. Some have suggested adopting HTML5 web cookies cookies like advertisers have been using for at least a decade in desktop browsers. The problem with this approach is that a web browser would have to be opened every time you install a new iPhone or iPad app to register your device, and there’s no way developers will implement that experience in the App Store unless they absolutely have to.
Mobile App Tracking, a company that boasts clientele like Zynga and LivingSocial, has proposed device fingerprinting. This approach is rather scatterbrained, as it needs apps to collect various bits of data about your iPhone (location, IP address, iOS version, etc.) and combine them together into one unique identifier. Unfortunately, users cannot easily opt out of fingerprinting or reset their device fingerprint altogether. There’s plenty of room for discrepancies since all of these bits of data can be meshed together and lose their accuracy over time. Device fingerprinting also requires licensing fees, so don’t expect it to gain widespread adoption.
Promising Alternatives
Cross-platform gaming network OpenFeint is offering the OFUID to game developers. Users can create an OpenFeint login and sign into supported App Store games, thereby giving those connected games access to that device’s OFUID. It makes tracking and advertising easier for apps on the OpenFeint network. The problem is that the OFUID clearly only applies to mobile gaming.

As Appsfire is both a developer of consumer apps and an ad network, we sought a UDID replacement but were not interested in a solution owned by any single provider. We also foresaw a fragmented market where UDID management was operated by multiple providers with no cooperation between them.
Appsfire’s OpenUDID has perhaps been the most covered UDID replacement in the press. The mobile app marketing platform made headlines out of the gate when it announced its open source initiative to offer a universal unique identifier. OpenUDID is slightly different from a MAC address or UDID, but it does carry similarities. The solution uses iOS’s clipboard function to essentially copy and paste tracking data between apps, which is actually an unintended use of APIs. There’s the small potential that a third-party could also silently intercept the data during the copy and paste, according to mobile ad platform MoPub. However, despite the fact that one universal identifier is still given to each device, OpenUDID does address privacy infringement concerns better than most of its competitors.
A Solution That Makes Sense

Wayne Chang and Jeff Seibert are the co-founders of Crashlytics, a team of 8 that does iOS crash analysis. They plan to also branch out and support Android in the near future. Crashlytics is responsible for another open source UDID alternative called SecureUDID.
When an iOS app crashes (over a billion crashes happen ever day), developers need to know what caused the problem. Jeff Seibert realized this while he was working at Box as the head of Apple software development. One day he injected some code into one of his lesser-known apps to make it send back a report detailing each crash. He woke up the next morning with over 6,000 crash reports on his server. And so Crashlytics was born.
Code from Crashlytics is used to send crash reports and perform analysis so that developers can determine what is causing their apps to crash. Seibert, who also gained experience in marketing and engineering at Apple, told Cult of Mac that his company had been using the UDID to distinguish between specific devices that were crashing, highlighting the functionality that Apple provided with the UDID. “If we can correlate a given user across apps, we can maybe identify that the user’s device is broken and not a specific app,” explained Seibert. “On what other platform in the history of computing could you do this?”
When asked why his company made SecureUDID, Seibert said, “We wanted to try and solve the root problem of why Apple started rejecting apps. And in our minds it came down to the potential for privacy infringement.”
It’s important to note that there’s been some drama between OpenUDID and SecureUDID. Appsfire claims that the guys at Crashlytics were originally for OpenUDID last year when it was first proposed and that SecureUDID is essentially based off OpenUDID code. Both projects have been open-sourced, but Appsfire feels like Crashlytics has violated the etiquette of the open source community. Here’s what Appsfire had to say:
SecureUDID actually serves a different purpose than OpenUDID: it helps developers create a unique and persistent UDID, shared within the same namespace (app or developer): ok for analytics. What SecureUDID doesn’t do is let this token be accessed by a 3rd party app: useless for advertising.
While Appsfire states that SecureUDID cannot be used effectively for advertising across apps, Crashlytics states explicitly that SecureUDID can work with ad networks on its website. You can read the full response to Appsfire on the Crashlytics blog.
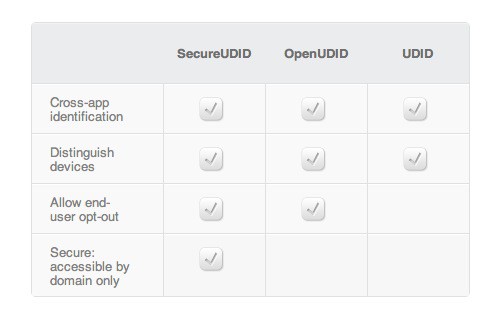
Unlike OpenUDID, SecureUDID does not give each iOS device a universal unique identifier. Instead, a secure unique identifier is only created for a given company. “We wanted to break the assumption that there was one identifier per device,” explained Seibert. “With SecureUDID, a big ad network gets a unique ID for every device it touches, but another ad network gets a different ID. If one leaks, it doesn’t affect the others.”
This approach means that your iPhone merely has an account number instead of a social security number. If your personal data leaks, SecureUDID compartmentalizes the possible privacy infringement. Everyone would also know where the leak came from, as there would be multiple IDs for your device tied to different companies.
“I think it’s a very natural improvement of what they’re [Appsfire/OpenUDID] are offering. At a high level, they’re not much better than Apple’s UDID because they are binding a single value to your device,” Seibert told Cult of Mac.
For instance, Path 2.1.1 for iPhone recently shipped with Crashlytics for crash analysis and SecureUDID as a UDID replacement, according to Seibert. Apps like Expedia, Yammer and Groupme are also using SecureUDID already. With the way the landscape looks now, OpenUDID and SecureUDID should be competing as UDID replacement standards for the next several months.
Conclusion
Apple has been silent all these months as its forced its ‘App Economy‘ to move away from the UDID. Hopefully the company will address the issue at its Worldwide Developers Conference this summer. Developers, Seibert included, also hope that Apple will detail new means of ensuring user privacy and raising awareness in iOS itself with prompts and opt-ins.
While the timeline is short for Apple, it seems possible that an official UDID replacement will be introduced this year as well. In the meantime, the way our iPhones handle our data is changing and evolving. And ultimately, we are responsible for what personal information we share with the world.
![What Is A UDID And Why Is Apple Killing Apps That Track Them? [Feature] This unique string of alphanumeric text attached to every iPhone and iPad is the source of a lot of privacy concerns.](https://www.cultofmac.com/wp-content/uploads/2012/04/Screen-Shot-2012-04-17-at-11.43.29-AM.jpg)


6 responses to “What Is A UDID And Why Is Apple Killing Apps That Track Them? [Feature]”
But there is still a way to get UDID from device without iTunes: http://get.udid.io (because iOS developers still need it)