The Central Intelligence Agency has been using malware to spy on iPhone and Android users, according to the largest-ever publication of confidential documents from WikiLeaks — and the spy tools are now in the hands of others.
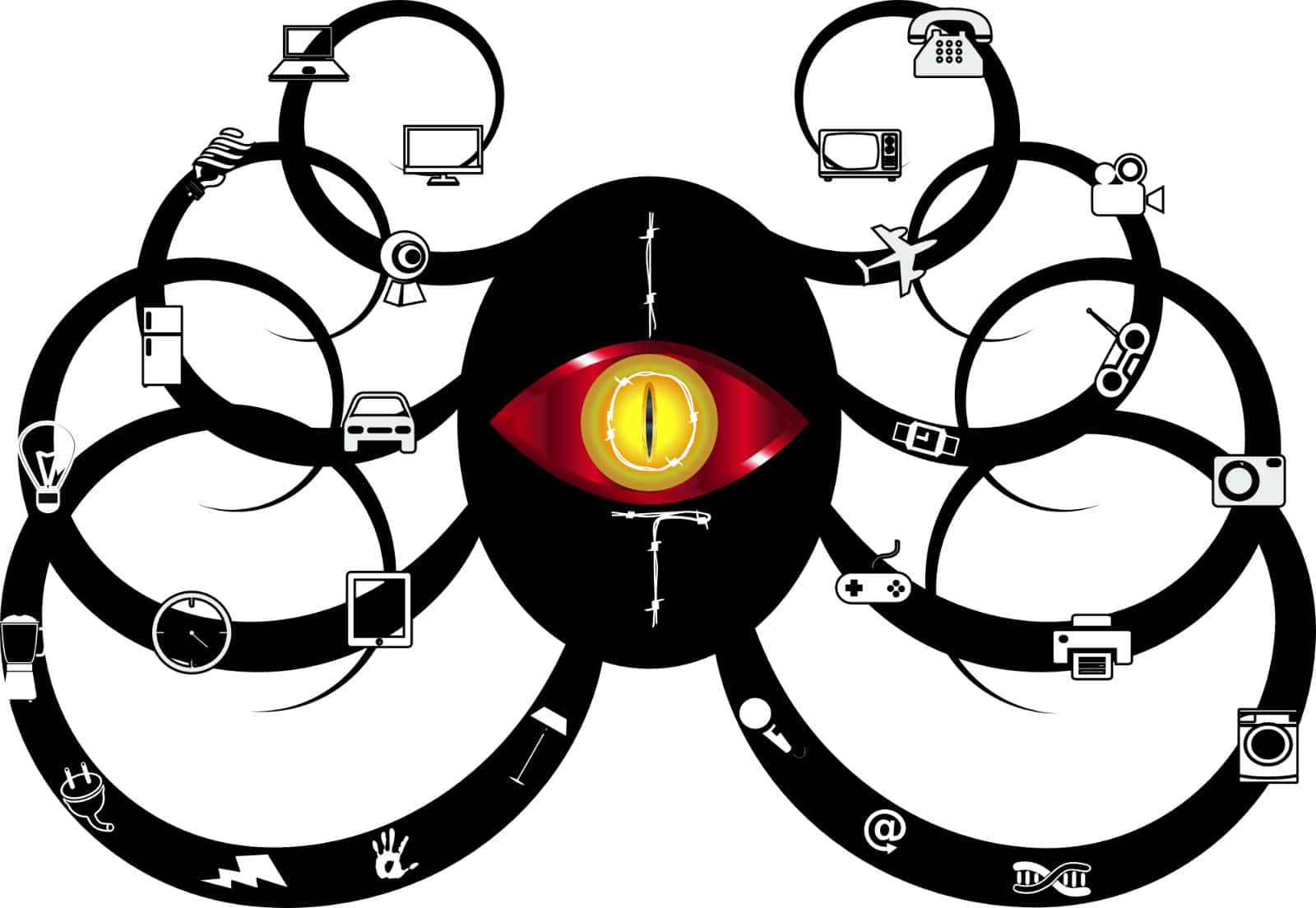
As part of a covert hacking program, the CIA created a “malware arsenal” and dozens of “zero day exploits” to infiltrate smartphones, tablets and even smart TVs to extract data and turn them into covert microphones.
But the agency recently lost controls of these tools. Those who have obtained them now have “the entire hacking capacity of the CIA” at their disposal, according to WikiLeaks.
The “Year Zero” series from WikiLeaks is comprised of a whopping 8,761 documents and files allegedly taken from a high-security network at the CIA’s Center for Cyber Intelligence (CCI) in Langley, Virginia. It details a catalog of malware, viruses, trojans and more created to spy on the agency’s targets.
The collection accounts for hundreds of millions of lines of code, according to a confidential archive that has been circulated among former U.S. government hackers. One of them provided WikiLeaks with some of the documents, which reveal the frightening breadth and power of the CIA’s hacking efforts.
CIA’s hacking tools target iPhones, Samsung smart TVs and more
At the end of 2016, the CIA’s hacking division was made up of more than 5,000 “registered users” who had produced over a thousand tools to infiltrate target devices throughout Latin America, Europe and the United States.
Its Engineering Development Group (EDG), a division within the CCI, was responsible for developing and supporting all “backdoors, exploits, malicious payloads, trojans, viruses and any other kind of malware used by the CIA in its covert operations world-wide.”
One hack, developed alongside the United Kingdom’s MI5 security service, was designed to put Samsung smart TVs into a “Fake-Off” mode. This led the owner to believe the TV was in standby mode when, in actual fact, its microphone was recording voices nearby and sending them to the CIA over the internet.
iOS devices were also a major target. The CIA created and obtained tools from GCHQ, NSA, FBI and contractors like Baitshop that allowed them to bypass the encryption used by apps like WhatsApp and Telegram and collect audio and text message data.
It has also created tools that turn these devices into discreet microphones, and others that allow them to be controlled remotely. Infected phones can send information like location data, camera recordings and audio back to the CIA without detection.
Similar tools were developed for Android and Windows phone devices, and there has been a “very substantial” effort to infiltrate Windows on desktops, macOS and Linux, according to Wikileaks.
If just one of the CIA’s tools becomes “loose” and makes its way into the wild, it can be used by other states, the “cyber mafia” or the average teenage hacker. And according to WikiLeaks, the CIA has lost control of it all.
CIA lost control of its hacking tools
“Recently, the CIA lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized ‘zero day’ exploits, malware remote control systems and associated documentation,” reads a press release published today.
“This extraordinary collection, which amounts to more than several hundred million lines of code, gives its possessor the entire hacking capacity of the CIA.”
The documentation also reveals how the CIA “hoarded” serious software vulnerabilities so they could be exploited later, despite a commitment from the Obama administration that the agency would disclose any “zero day” bugs to U.S. companies on an ongoing basis.
“As long as the CIA keeps these vulnerabilities concealed from Apple and Google (who make the phones) they will not be fixed, and the phones will remain hackable,” said WikiLeaks.
These vulnerabilities don’t just exist on our smartphones. They also exist on those used by members of Congress, top CEOs and other high-ranking officials. And if the CIA can find and exploit them, others can. WikiLeaks says many of the hacking tools may have already been used by rival agencies or cybercriminals.
“Cyber ‘weapons’ are not possible to keep under effective control,” the site warns. “Cyber ‘weapons’ are in fact just computer programs which can be pirated like any other. Since they are entirely comprised of information they can be copied quickly with no marginal cost.”
The number of documents and files contained in this leak, which date back to 2013, eclipses the total number of pages published over the first three years of the Edward Snowden NSA leaks. Everything can be downloaded from the WikiLeaks website.


2 responses to “WikiLeaks: CIA lost control of its iPhone hacking arsenal”
Greaaaaaaaat
Thanks for sharing…..and thank you cia,love the rf technology you’ve giving me :}