Hackers have just given iPhone and iPad users a big reason to upgrade to iOS 9 due out later today: it fixes a serious AirDrop security vulnerability.
Mark Dowd, an Australian security researcher with Azimuth Security, revealed this morning that iOS 8.4.1 contains a critic security flaw in AirDrop that could allow an attacker to install malware on any device within range. Worst of all, even if a victim tried to reject the incoming AirDrop file, the bug lets attackers tweak the iOS settings so the exploit will still work.
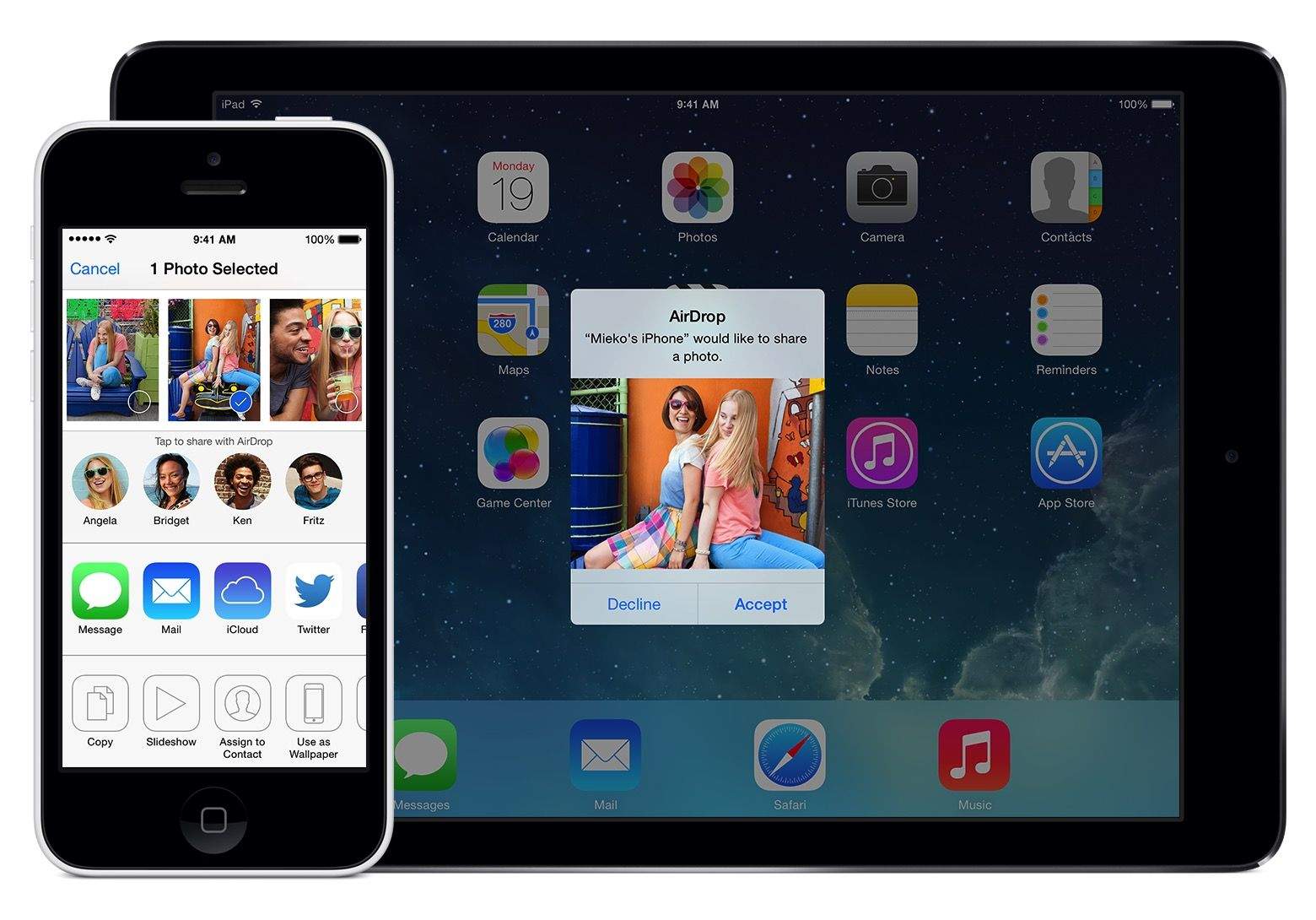
Check out the lethal bug in action:
To make sure you’re not vulnerable to the attack, all users should update to iOS 9 and OS X El Capitan ASAP (are we sure this isn’t just a hell of a marketing ploy by Apple?).
The AirDrop bug affects iOS 7 and all version upward, as well as OS X Yosemite. The hack uses a ‘directory traversal attack’, according to Forbes, who spoke with Dowd Wednesday morning. Hackers use the attack to enter sections iOS they shouldn’t have access to, but Dowd found it’s possible to exploit AirDrop, and then alter files so that iOS will accept any software with an Apple enterprise certificate.
Apple uses enterprise certificates to allow businesses to install apps not found on the App Store. Dowd found that he could trick iOS into believing his enterprise certificate was from a trusted user when it shouldn’t have been. He then installed his malware into the third party apps directory and even found a way to replace the Phone app with his malicious app. Then the iPhone just has to reboot and the attack is done.