Heartbleed sent the web reeling with the discovery that the catastrophic security hole quietly left passwords and other private data open for the taking on nearly 66% of the Internet’s servers. Luckily for Apple customers, iOS and OS X were never vulnerable to Heartbleed but some of the most popular sites and services on the Internet weren’t so lucky.
Many companies are still working to patch their hole, but Mashable has compiled a list of the biggest sites hit by Heartbleed. There’s no way to tell if your info was actually snatched by attackers, but if you have account on the following sites that were affected and subsequently patched, you should change your password ASAP:
- IFTTT
- Tumblr
- Yahoo
- Gmail
- Amazon Web Services
- TurboTax
- Dropbox
- OKCupid
- SoundCloud
- GoDaddy
- Minecraft
Source: Mashable


19 responses to “Change Your Passwords For These 15 Heartbleed-Vulnerable Sites ASAP”
If I am on OSX and iOS, do I still need to change my password for these sites? I apologize for this noobish question.
Yes, this bug is not OS-specific.
Unfortunately the article tells the story like it is the usual Windows only problem. “Luckily for Apple customers, iOS and OS X were never vulnerable to Heartbleed”
Most Android devices are vulnerable, so it actually is the usual problem.
Yes, you do need to change your password. The error was on the server side not on the client side
ok thanks guys
Correct me if I’m wrong, but if the virus is server-side and acquires encryption keys, then changing your password wouldn’t do anything whatsoever…
We don’t want to change the passwords until the servers have been patched. The list above are sites that have their servers patched.
We don’t want to change passwords for sites that are still vulnerable because a nasty actor could still leach out your passwords. And it ISN’T a virus, it’s a flaw.
the 15 sites listed have already updated their servers to fix the hole.
Facebook has not re-issued their SSL certificate, so its better to wait till that happens before changing your password there.
It isn’t a virus… It doesn’t spread from computer to computer. After administrators of servers patch the vulnerability they will generate new encryption keys, but your data may have already been stolen so bad guys might have your password and could still use it to access your account.
it’s not a virus, it’s an exploit.
Also passwords are generally hashed, not encrypted. Heartbleed dumps memory so it’s possible that your hashed password was dumped. The encryption keys only make it possible to decrypt ssl data (making ssl useless for the site until they get new keys). So changing your password will make it so that if they break the hashed password, your account won’t be vulnerable.
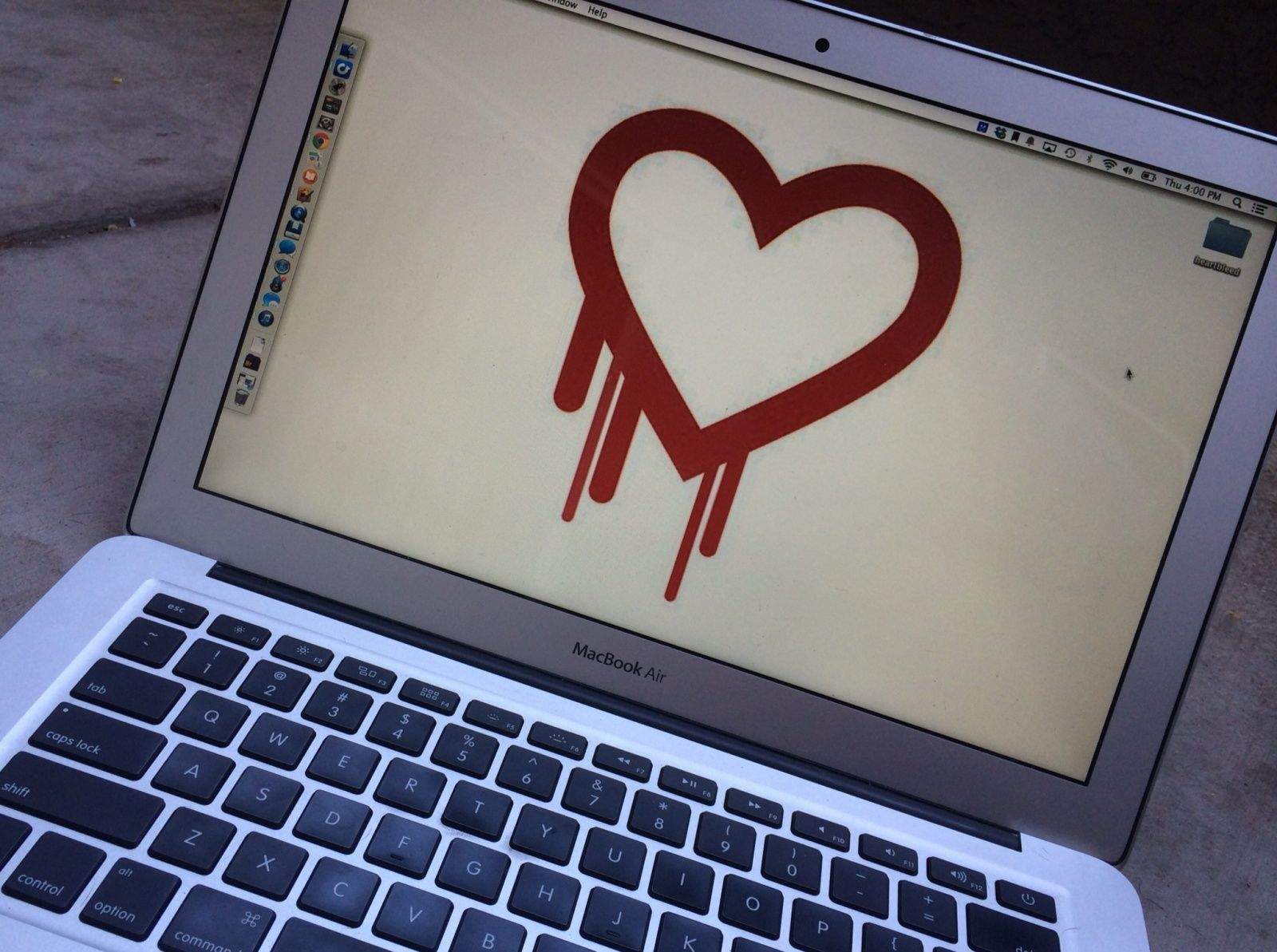
Why is this logo so prevalent?
The logo was created as such as it clearly represents the name of the bug, “Heartbleed”. As for why it got its name, I don’t know.
The bug is in openssl’s implementation of the TLS heartbeat feature, so they’re calling the bug heartbleed.
If you haven’t visited a site in a while I don’t really see the point of changing your password. For example my password for turbo tax which i haven’t logged into in months wont still be in memory on the servers. I guess there is a chance that someone was exploiting the vulnerability before it was made public but in that case you should probably change all your passwords everywhere.
The exploit has been known about for two years, it’s just now being made public.
The bug has existed in the current versions of open ssl for a bout 2 years. Neel Mehta reported it fairly recently and the CVE was released on 4/7/2014. We didnt start seeing scans for this vulnerability on our network until about 2 days ago.
Is it necessary to change my passwords, if I use Sticky password (password manager)? Thanks for your advice.