The Pegasus spyware, developed by Israeli firm NSO Group, has successfully been avoiding security new measures built into iPhone to block such attacks.
One version of the “zero-click” exploit was installed on an iPhone 12 Pro belonging to a Bahraini human rights activist, despite the fact that the device was running recent versions of iOS 14 with Apple’s “BlastDoor” protection.
BlastDoor is a security feature baked into iOS 14 that is designed to prevent spyware attacks by filtering out malicious data distributed through iMessage. Apple has continued to improve upon it since its introduction.
It seems, however, that despite the feature’s enhancements, attackers are still finding ways to avoid BlastDoor’s protections. Citizen Lab has discovered a Pegasus strain that worked successfully under iOS 14.4 and iOS 14.6.
New Pegasus attacks avoid iPhone’s BlastDoor shield
“Starting in February 2021, we began to observe NSO Group deploying a new zero-click iMessage exploit that circumvented Apple’s BlastDoor feature,” reads the Citizen Lab report. “We refer to the exploit as ForcedEntry.”
“We saw the ForcedEntry exploit successfully deployed against iOS versions 14.4 and 14.6 as a zero-day. With the consent of targets, we shared these crash logs and some additional phone logs … with Apple.”
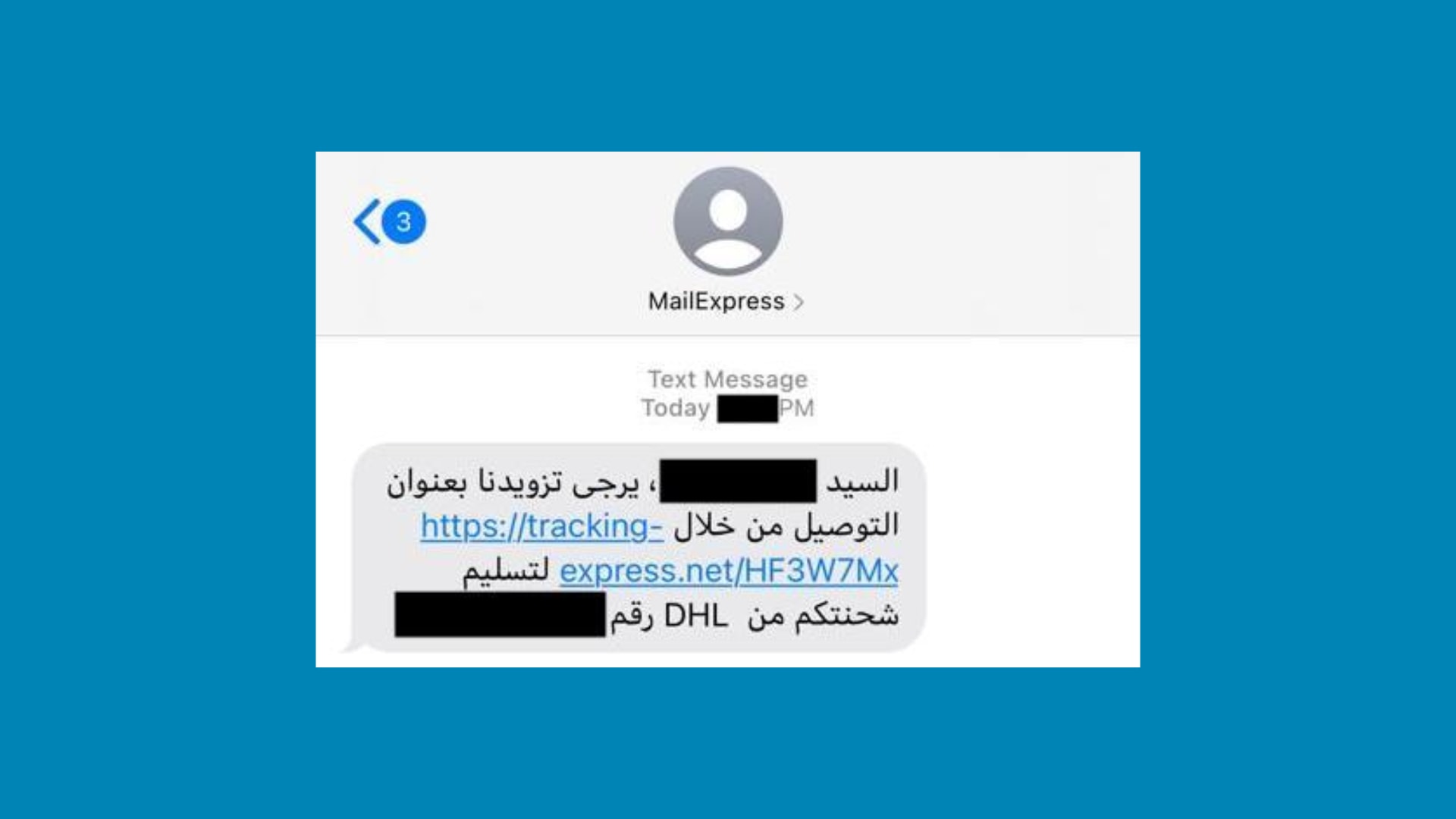
Apple told Citizen Lab it is investigating the ForcedEntry exploit, and an earlier variant called Kismet. Both are distributed through text message, like other Pegasus attacks, and require no input from the user for installation.
Apple and its users won’t be pleased to learn that Pegasus attacks are circumventing the BlastDoor feature designed to block them. But Apple told TechCrunch that it has other protections in place to secure iMessage.
iOS 15 strengthens iPhone’s defenses
Apple has “strengthened its defenses” in iOS 15, scheduled to make its public debut this fall, the report reads. However, Apple did not provide additional details on the steps it is taking to protect against Pegasus going forward.
Of course, only time will tell whether those defenses are enough to prevent new strains of Pegasus in the future. But it is certainly concerning that the attacks have already found ways around BlastDoor.
An earlier leak revealed Pegasus is currently being used by a number of governments worldwide, including those in Bahrain, Mexico, Saudi Arabia, and the United Arab Emirates. NSO Group won’t comment on its clients.
Five of the targeted Bahrainis who worked with Citizen Lab found their phone numbers on a list of 50,000 people targeted by Pegasus around the world.