A consultant has discovered an unpatched security bug in iOS that prevents virtual private networks from encrypting all traffic.
The problem impacts iOS 13.3.1 and later and could lead some internet connections to expose data or leak IP addresses.
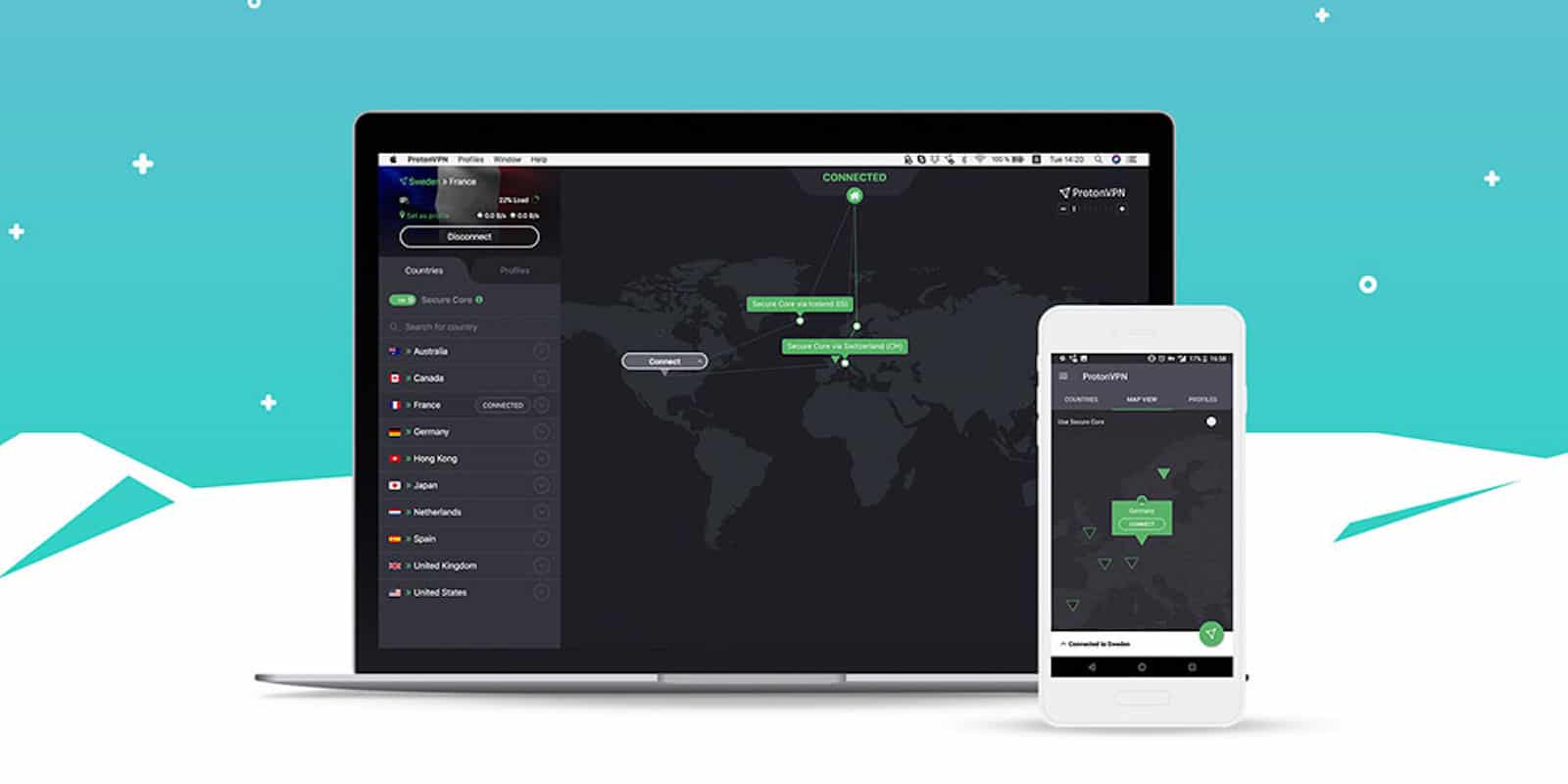
The bug was discovered by a security consultant for ProtonVPN, which recently raised alarm in a blog post.
Connection to a VPN on iOS isn’t directly impacted by the bug, according to the Swiss-based Proton. Connections prior to activating a VPN seem to remain outside the tunnel securing the personal network.
A patch will have to come from Apple because it does not allow a VPN app to kill existing network connections.
Proton recommends enabling and disabling Airplane Mode after connecting to a VPN. This may kill other network connections, though Proton said it doesn’t always work.
“Most connections are short-lived and will eventually be re-established through the VPN tunnel on their own,” ProtonVPN said. “However, some are long-lasting and can remain open for minutes to hours outside the VPN tunnel.
“Those at highest risk because of this security flaw are people in countries where surveillance and civil rights abuses are common.”
Source: Bleeping Computer