Elcomsoft claims its iOS Forensic Toolkit can now extract certain pieces of data from an iOS device before it has been unlocked.
Almost all of the data stored on an iPhone or iPad is securely encrypted after a reboot or restart — until a passcode has been entered. But the little bit that isn’t, which includes keychain records, can now be obtained.
Apple has been making it harder to crack into iOS devices with every major software update. It is now near-impossible to gain access to a locked iPhone or iPad without special tools that cost hundreds of thousands of dollars.
But there might be some data you can obtain from an iOS devices without unlocking it. And Elcomsoft believes its iOS Forensic Toolkit can help.
Passcode locks can’t keep everything safe
The Toolkit can now be used to extract data from an iPhone or iPad in “Before First Unlock” (BFU) mode. This is the state your device is in after a reboot or restart, before it has been unlocked for the first time.
“In Apple’s world, the content of the iPhone remains securely encrypted until the moment the user taps in their screen lock passcode,” Elcomsoft explains.
Only upon entering the correct passcode is an encryption key generated. And only when an encryption key is generated can local data be decrypted. But not everything is completely under lock and key during this time.
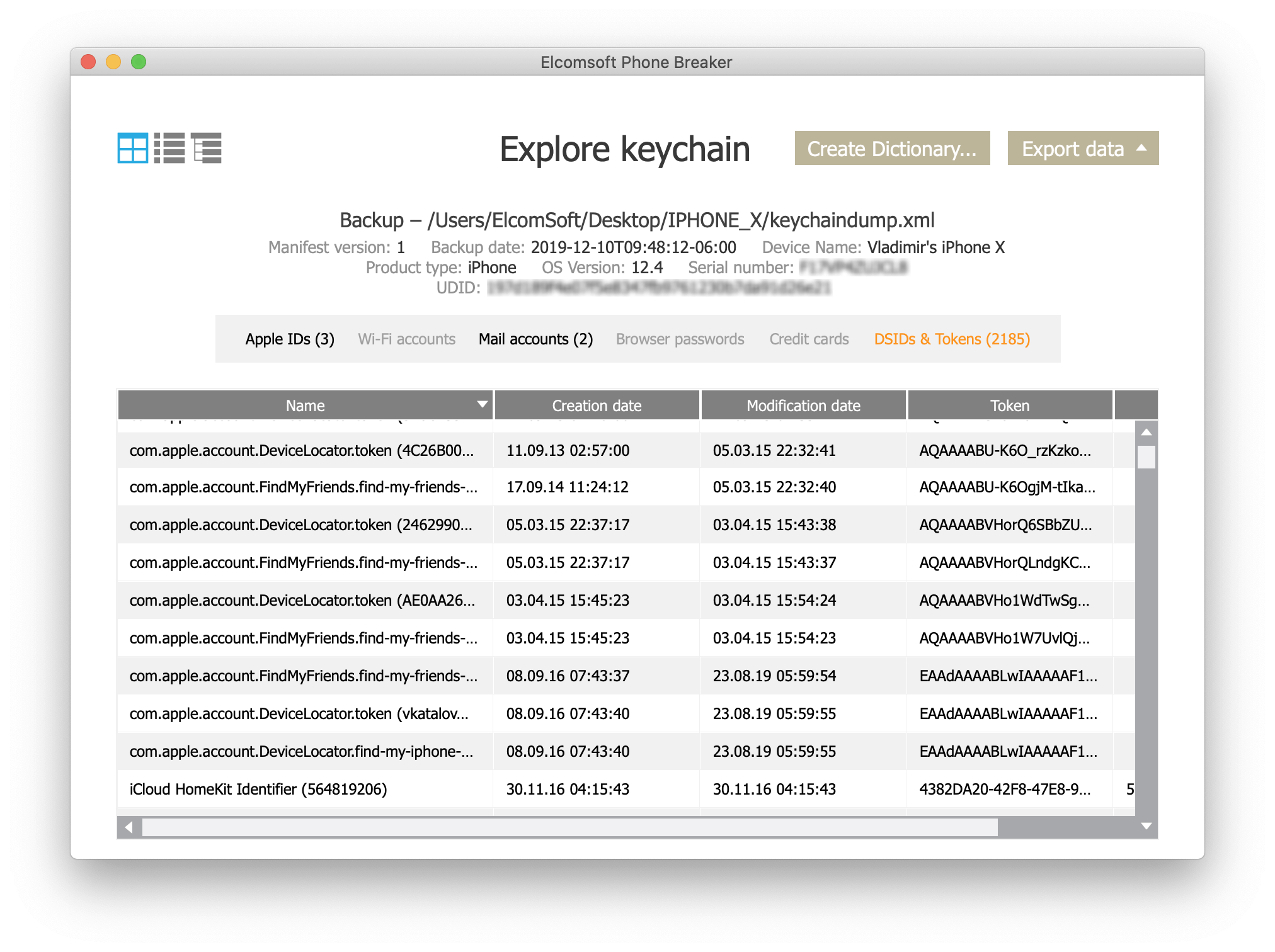
“We’ve discovered that certain bits and pieces are available in iOS devices even before the first unlock,” Elcomsoft adds. And those “bits and pieces” can include sensitive keychain records, such as account passwords.
Why isn’t everything encrypted?
Apple would decrypt every single morsel of data if it could. But the pieces that aren’t secured were not left out accidentally; they must be kept open to allow an iOS device to boot up correctly before a passcode is entered.
If your device is jailbroken, even more of your data, including system files, is left unsecured. The iOS Forensic Toolkit allows that data to be extracted even when a device has been disabled.
“While this is only a partial keychain extraction, as most keychain records are encrypted using the key derived from the user’s passcode, this is much better than nothing – and coming from a locked device!”
Extracted data can also include a list of installed apps, some Wallet information, a list of Wi-Fi connection, “a lot” of media files, notifications, and location points.
iPhone 11 is immune
Elcomsoft can’t help you unlock an iOS device — and it doesn’t want to. But it is offering “other possibilities” that allow certain data to be obtained without complete access to an unlocked iPhone or iPad.
The iOS Forensic Toolkit is said to work with iPhone 5s through iPhone X, regardless of the software version they are running. It does not work with more recent handsets, like iPhone XS and iPhone 11.
We should also point out that the iOS Forensic Toolkit tends to be used more commonly by law enforcement and government agencies, rather than the average Joe. But anyone can purchase a copy for $1,495.