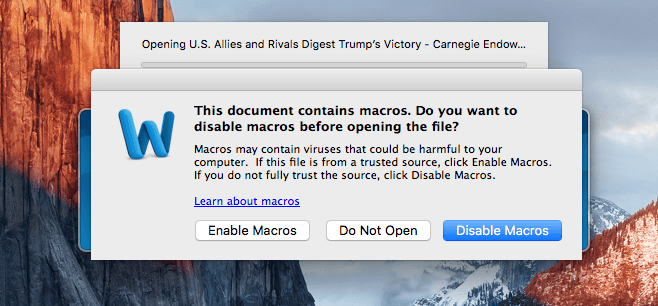
After spreading viruses among Windows PCs for years, malicious Microsoft Word documents are now infecting Macs.
The files contain a macro that silently executes in the background and downloads an application that can monitor webcams, steal passwords, read browser history and more.
Macro malware has been targeting PC users for well over a decade. Though the number of attacks has fallen, there has been a resurgence of malicious macros in recent years — mostly due to the fact that they are so effective.
That’s because the malware goes undetected for so long. When buried inside a Word macro — a seemingly legitimate piece of software — the malicious code doesn’t set off any alarm bells until a virus has successfully been installed and the damage has been done.
Mac malware on the rise
Mac users never had to worry about this in the past, but that’s no longer the case. Security researchers have now discovered the first Mac virus that stems from a malicious macro buried inside a Word document, reports Ars Technica.
The document is titled “U.S. Allies and Rivals Digest Trump’s Victory – Carnegie Endowment for International Peace.” When opened in Word that’s configured to allow macros automatically, it carries out its attack.
First, the software checks to ensure that the LittleSnith security firewall isn’t running. It then downloads an encrypted payload from securitychecking.org and decrypts it using a hard-coded key. Finally, the payload is executed and the virus is active.
The payload is no longer being served, so researchers were unable to determine exactly what it did. However, the open-source framework it is based on has a number of capabilities, like the ability to monitor webcams, take encrypted keys from Keychain and more.
It is thought this particular malware wasn’t very advanced, but Word macros have been able to cause carnage in the past. Just over a year ago, a malicious macro was responsible for a virus that left 225,000 Ukrainian homes without electricity.
“By using macros in Word documents, they are exploiting the weakest link; humans!” wrote Patrick Wardle, director of research at Synack, which first stumbled across the Mac malware. “And moreover since macros are ‘legitimate’ functionality (vs. say a memory corruption vulnerability) the malware’s infection vector doesn’t have to worry about crashing the system nor being ‘patched’ out.”
Mac malware still has some way to go before it’s as mainstream as Windows attacks, but as Apple’s platform becomes increasingly popular, there’s no question it is catching up.


4 responses to “New Mac malware targets Microsoft Word users”
Mac users tend to be much easier to fool, as they bought into Apple’s ecosystem .So much easier targets as many of them still believe wrongly Macs are secure by default.
On a secure scale of 1 to 10, Macs are 1 and Windows are 8. 99.9% of malware is written for Windows.
Windows is much more hardened than any Mac, Apple relied on “security through obscurit”‘ to their downfall.
…and it comes as no surprise that this particular virus relies on a MICROSOFT product as its origination. PC = Perpetual Crap.