Another study of the bring your own device (BYOD) phenomenon concludes that the trend of employees bringing the personal iPhones, iPads, and other devices into the office shows no sign of slowing down. It also confirms previous reports that indicate many personal devices being used in the workplace don’t have even basic security features enabled.
The study by Coalfire, a company the specializes in IT risk management services, paints a particularly grim picture of the lack of security for iOS and Android devices in the workplace. With the BYOD trend show no signs of slowing or ending, Coalfire CEO Rick Dakin, notes that companies cannot afford to keep ignoring mobile security concerns.
The BYOD trend is not slowing down, and while it has many benefits, it’s also introducing a number of new security risks that may be foreign to many companies. The results of this survey demonstrate that companies must do much more to protect their critical infrastructure as employees work from their own mobile devices, such as tablets and smartphones, in the workplace. Companies need to have security and education policies in place that protect company data on personal devices.
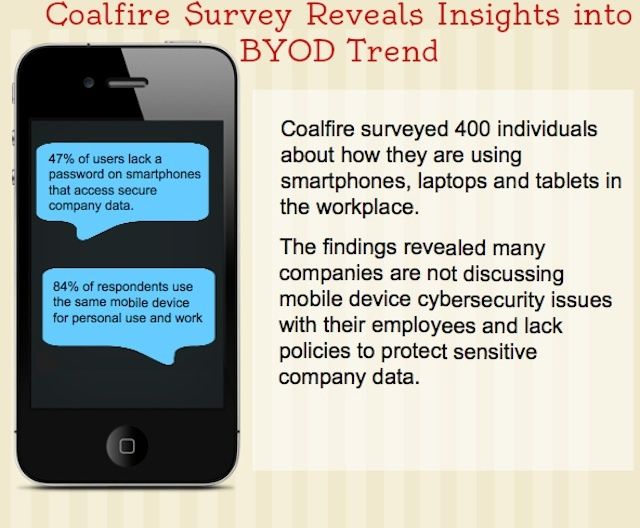
Coalfire surveyed 400 individuals working in a range of industries across North America and found that 84% of employees rely on a single smartphone for both work and personal use. The survey found several concerning statistics about the devices used by those employees.
- 47% reported they have no passcode on their mobile phone
- 36% reuse the same password
- 60% are still writing down passwords on a piece of paper and 7% store passwords in an unsecured document on their Mac or PC
As disturbing as that last piece of data is, it was accompanied by some good news as about one-quarter (24%) of respondents report using password manager apps while 11% said that they store passwords in an encrypted document on their computer.
While that is disturbing news it does seem to fit with Coalfire’s findings about how proactive IT departments are being about mobile security and personally-owned devices.
- 49% stated their IT departments have not discussed mobile/cyber security with them
- 25% said that they had been briefed about security and password concerns by their IT department
- 18% worked for businesses without an IT department (presumably for smaller organizations without the need or resources for a dedicated staff
- 8% said they weren’t sure if an IT staff member had discussed security issues with them
- 51% clamed that their companies do not have the ability to remotely wipe data from mobile devices if locked, lost, or stolen
- 21% said that their companies did have the ability to remotely wipe their devices
- 28% didn’t know if their IT department could remotely wipe a device or not
The study also uncovered similar results when it comes BYOD policies.
- 37% said their employer had a formal policy of some type in place and an equal number (37%) said their employer did not have a policy in place
- 26% said they weren’t sure if there was a BYOD policy
Asked who they would contact about a lost device, the majority (56%) said they didn’t know or weren’t sure. 15% said they would call their mobile carrier. Just under a third (29%) said they would call their company or IT department.
The key lesson here is that IT departments, senior executives, department managers, and even HR staff need to take a much more proactive role in engaging staff about their mobile device use. That engagement needs to include explicit education about policies, security risks, and potential actions that might be taken if users don’t follow security guidelines.
Source: Coalfire
Image: Coalfire