This MDM post is brought to you by Scalefusion.
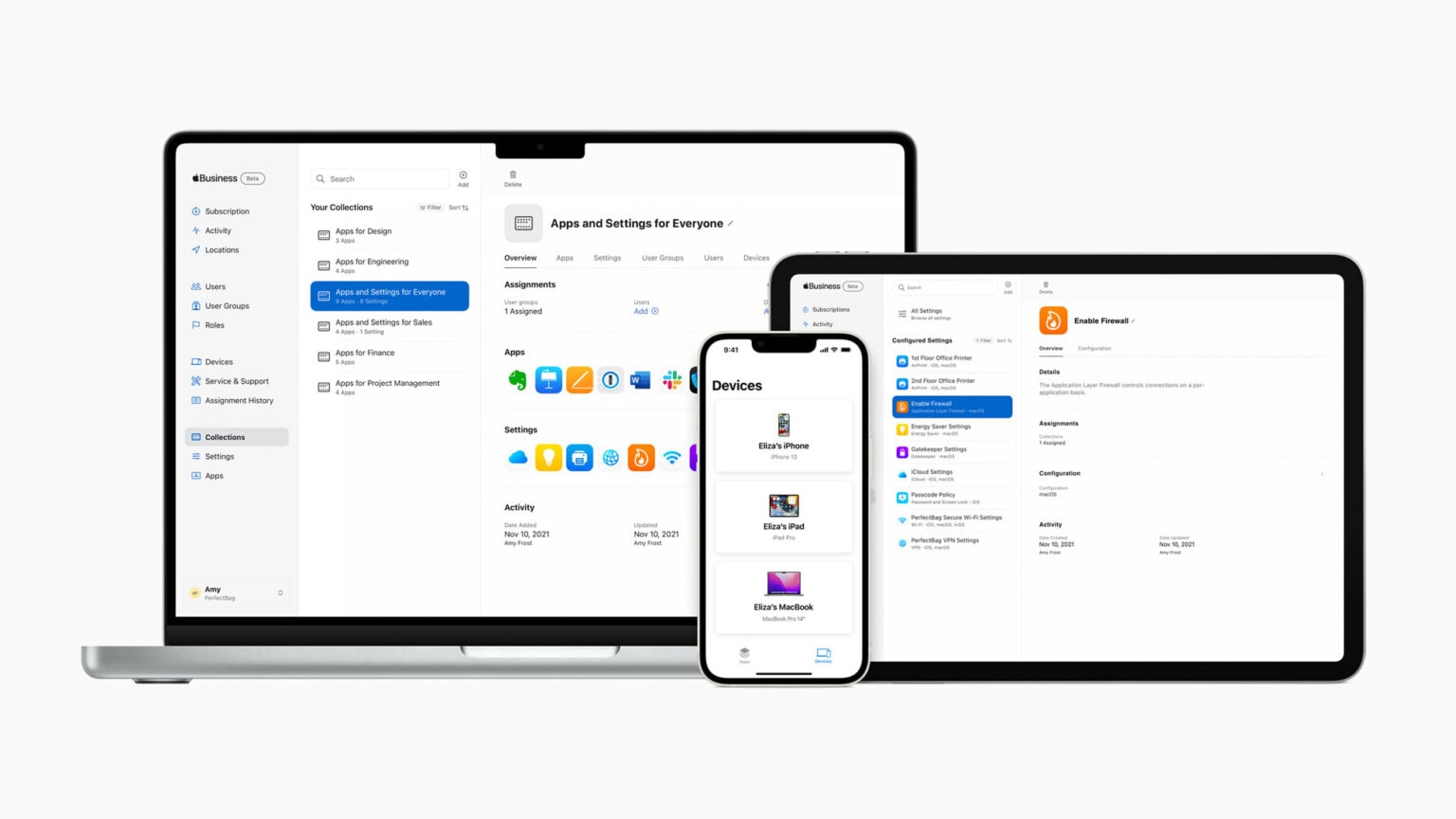
With the recent surge in employees working via smartphones, tablets and laptops from practically anywhere, it’s no surprise mobile device management, aka MDM, has become a crucial tool for organizations large and small. Then add in the growth of cloud computing and software-as-a-service (SaaS) apps, plus companies letting employees use their own devices (BYOD).
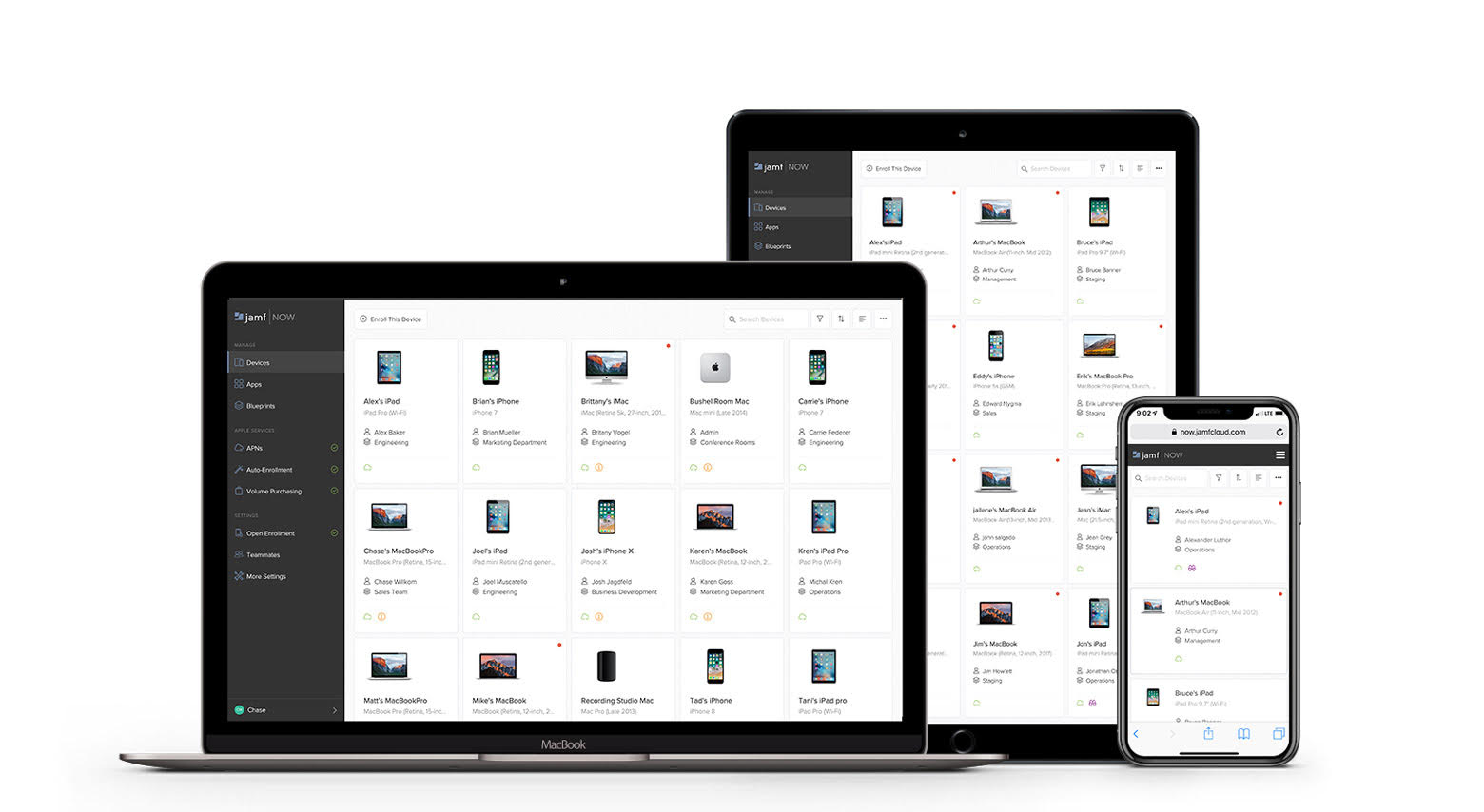
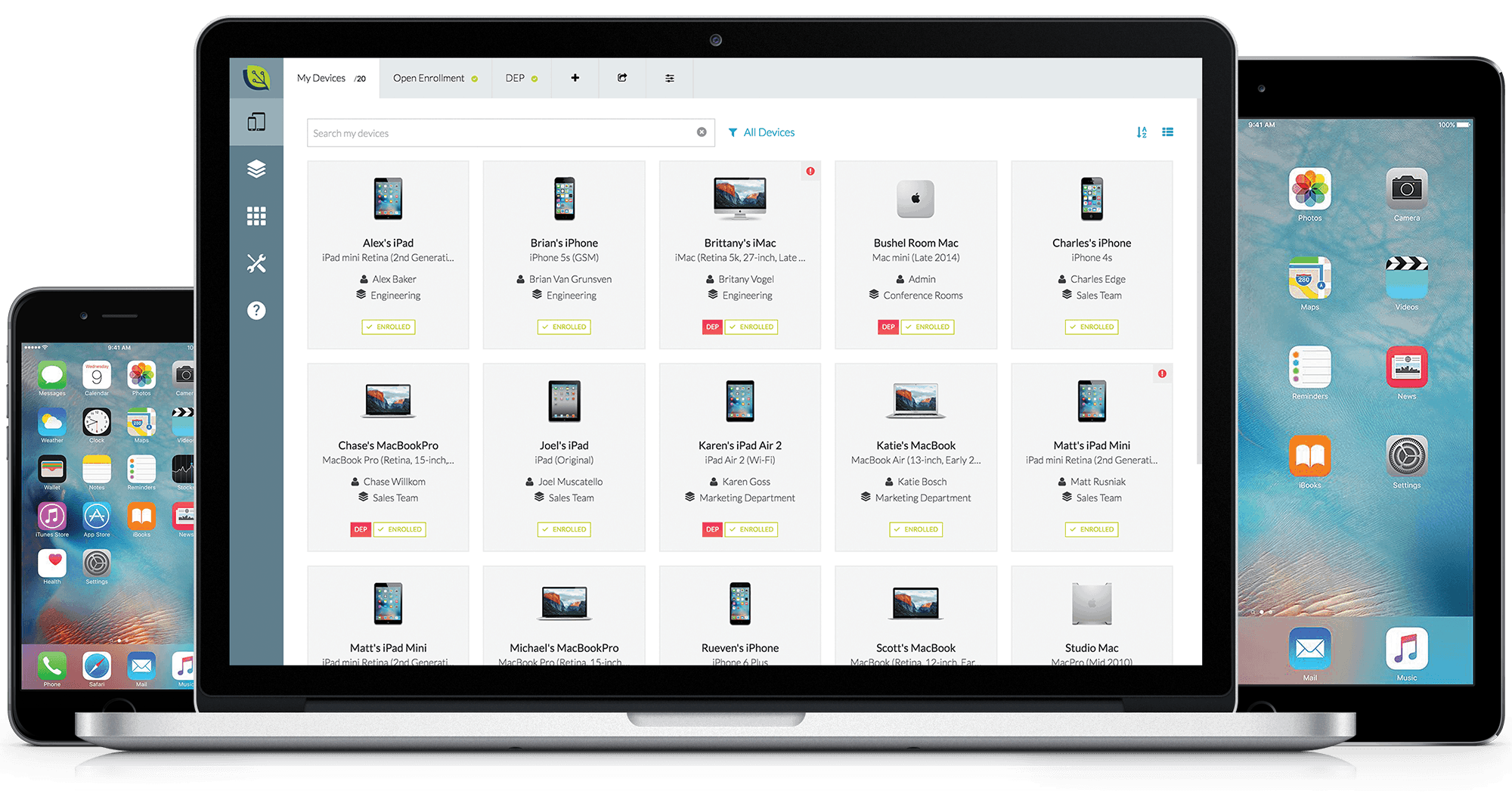
It all adds up to needing an MDM provider you can depend on. These days, you need something that serves the IT department’s needs while remaining easy for users to navigate. And it should work across operating systems and device types.
With Scalefusion, you can get up and running fast with a vast array of devices, and even expand your fleet, without having to worry about engaging multiple MDM providers.