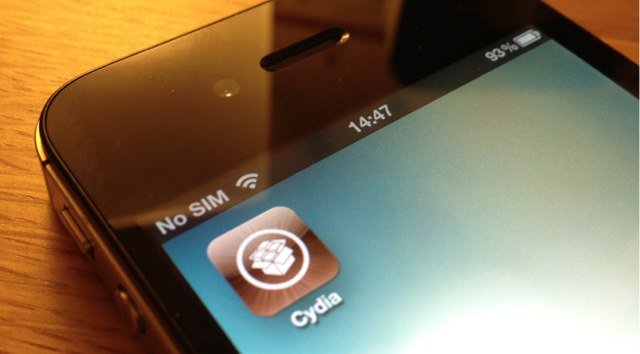
Regret upgrading to iOS 5.1 and losing your jailbreak? Yeah, me too. But thankfully, Pod2g and his team of iOS hackers have now discovered all of the exploits required for the iOS 5.1 jailbreak.
Hackers Find All The Exploits Needed For An iOS 5.1 Jailbreak
![Are You Telepathic? Incredible Hack Gives Siri The Ability To Read People’s Minds [Video] post-129416-image-b174f84bec0221dfbaf30f2b254ae1c6-jpg](https://www.cultofmac.com/wp-content/uploads/2011/11/post-129416-image-b174f84bec0221dfbaf30f2b254ae1c6.jpg)
![Siri Hacked To Run On The iPhone 4 And iPod touch 4G [Video] post-126898-image-48c8897bba506da660395e2373e4e7a3-jpg](https://www.cultofmac.com/wp-content/uploads/2011/10/post-126898-image-48c8897bba506da660395e2373e4e7a3.jpg)