Hackers have been able to gain unauthorized access to the MacBook Pro’s fancy new Touch Bar by taking advantage of a hole in Safari.
The duo demonstrated the exploit at the Pwn2Own security conference taking place in Vancouver, Canada this week and bagged $28,000 for their efforts.
The Touch Bar is powered by a dedicated T1 chipset and a custom version of watchOS. That T1 chip also manages the security of features like Touch ID and the MacBook Pro’s front-facing FaceTime camera. But it turns out it isn’t all that secure.
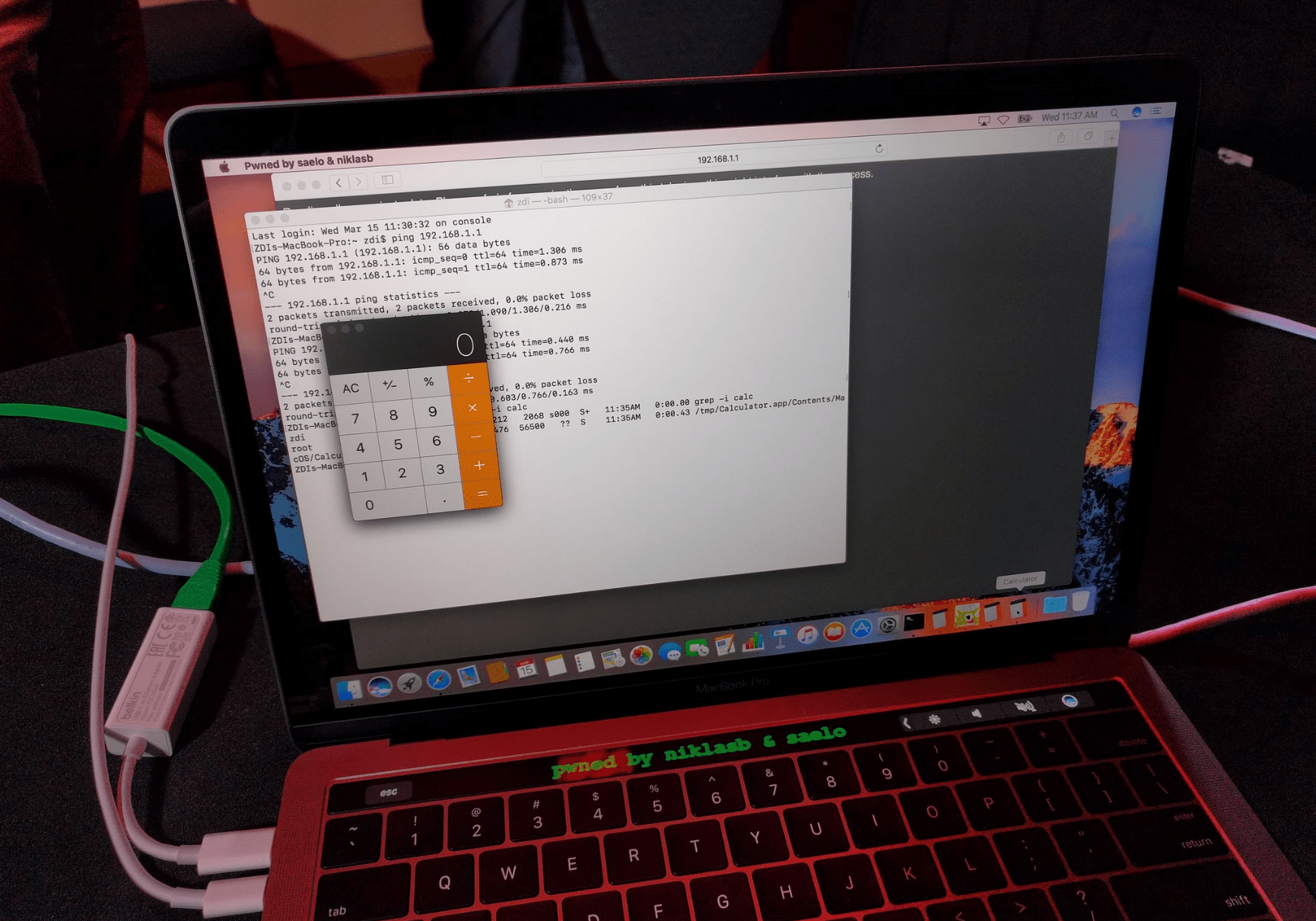
Using a number of logic bugs to exploit a vulnerability in Safari, Samuel Groß and Niklas Baumstark were able to gain access to the Touch Bar and display the custom message shown above, which reads, “pwned by niklasb and saelo.”
Although it was only considered a partial success, since the vulnerability has already been patched in more recent versions of macOS, the hack earned them a $28,000 reward and nine points in the Pwn2Own competition.
we had sep. exploits for 10.0.3 and 10.1. the 10.0.3 one is fixed upstream, so it counts as a duplicate
— Niklas B (@_niklasb) March 15, 2017
Another Safari vulnerability earned the Chaitin Security Research Lab a $35,000 reward and 11 points because it was seen as a full success. Other teams also attempted to breach Safari, Digital Trends reports, but were unable to do so within the allotted time.
Pwn2Own is giving away $1 million in prizes this year to those who are able to breach big platforms. Apple isn’t the only target; so far, others have successfully cracked the Linux kernel, Adobe Reader, and Microsoft’s new Edge browser for Windows 10.