The U.S. National Security Agency has spyware designed to grant backdoor access to the iPhone specifically, according to leaked documents shared by high-profile security researcher Jacob Appelbaum and German publication Der Spiegel.
While speaking at the Chaos Communication Congress in Germany, Appelbaum shared his knowledge of “DROPOUTJEEP,” a top-secret NSA program that can intercept an iPhone’s SMS messages, contacts, location, camera, and microphone.
Appelbaum, who has close ties to Wikileaks and NSA whistleblower Edward Snowden, prefaced his presentation at the conference by saying that his findings are “wrist-slitting depressing.” A 50-page catalog from the NSA reveals the organization’s backdoor tools for a host of companies, including well-known names like Cisco and Dell.
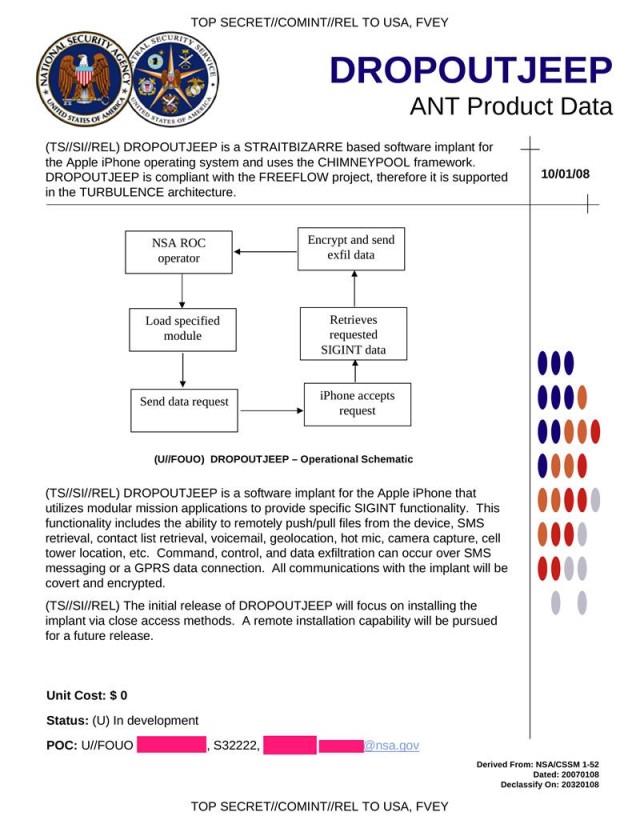
The iPhone’s backdoor is explained in a leaked NSA document:
“DROPOUT JEEP is a software implant for the Apple iPhone that utilizes modular mission applications to provide specific SIGINT functionality. This functionality includes the ability to remotely push/pull files from the device. SMS retrieval, contact list retrieval, voicemail, geolocation, hot mic, camera capture, cell tower location, etc. Command, control and data exfiltration can occur over SMS messaging or a GPRS data connection. All communications with the implant will be covert and encrypted.”
What is perhaps more alarming than the hack itself is the NSA’s claim that it will always succeed with installing the spyware on any iPhone. Physical access is needed now to install the spyware, but a version that can be remotely installed is in the works. It has been reported that the NSA has covertly intercepted hardware shipments before they arrive to their destinations in order to implant spyware.
“Do you think Apple helped them build that?”
“Do you think Apple helped them build that?” asked Appelbaum during his talk. “I don’t know. I hope Apple will clarify that… Here’s a problem: I don’t really believe that Apple didn’t help them. I can’t really prove it, but they [the NSA] literally claim that anytime they target an iOS device, that it will succeed for implantation. Either they have a huge collection of exploits that work against Apple products, meaning that they are hoarding information about critical systems that American companies produce and sabotaging them, or Apple sabotaged it themselves. Not sure which one it is. I’d like to believe that since Apple didn’t join the PRISM program until after Steve Jobs died, that maybe it’s just that they write shitty software.”
To be clear, this news doesn’t mean that Apple has indeed worked with the NSA on a backdoor for the iPhone like Appelbaum implies. But the NSA is confident it has a foolproof backdoor that gives a scary amount of access to someone’s iPhone.
After The Washington Post exposed the NSA’s PRISM program, Apple joined a group of other tech companies seeking for the NSA to be more transparent about its surveillance tactics. Tim Cook recently a joined a number of other executives to discuss the issue with President Obama.
You can watch Appelbaum’s full talk below, but the iPhone-related stuff doesn’t come up until about 44 minutes in:
We’ve reached out to Apple for comment on its knowledge of DROPOUTJEEP and will update this article if we get a reply.
Update: Apple has denied any knowledge of DROPOUTJEEP and the NSA’s efforts to create a backdoor into its products.
Source: Zero Hedge
Via: The Daily Dot


