An anonymous hacker who has exploited an iCloud security flaw that lets anyone unlock a lost or stolen iPhone says Apple contacted him about the matter today, but he deleted the email.
“They have asked me to contact [them] as quickly as possible, but why now?” the hacker, who goes by AquaXetine, said in an email to Cult of Mac. “I’ve already warned Apple couple months ago.” Cult of Mac confirmed that the email did in fact come from Apple.
The hack, which is the first of its kind, bypasses the iCloud security system for locked iOS devices called Activation Lock. By using the free DoulCi site, which appeared to be offline most of the day but is now back up, a locked iOS device can be tricked into thinking it’s talking to Apple’s iCloud servers when connected to a computer.
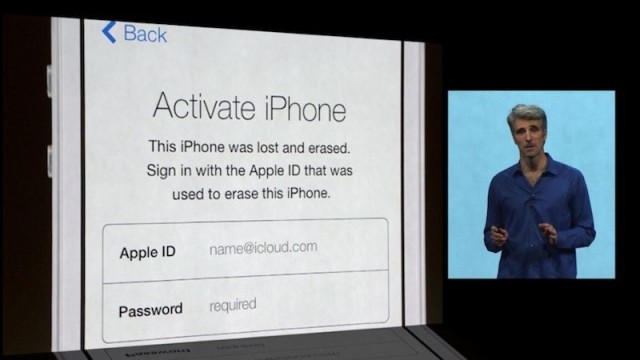
With iPhone theft accounting for about half the crimes in cities like San Francisco and New York, lawmakers are pushing legislation that requires all smartphones to have built-in kill switches. Activation Lock is Apple’s answer to the problem, a fail-safe introduced in iOS 7 to keep stolen iPhones and iPads from being usable. The system is designed to keep the contents of locked devices unreadable and unable to be erased without the user’s Apple ID.
Just deleted the mail from Apple ;) They are sooooooooo toooo late — AquaXetine (@AquaXetine) May 21, 2014
The hackers responsible for bypassing iCloud and Activation Lock, known by online pseudonyms AquaXetine and MerrukTechnolog, form Team DoulCi (roughly “iCloud” backward).
Their exploit, which they are labeling “the world’s first iCloud Activation Bypass,” involves adding just one line of code to the “hosts” file on a desktop computer. Instructions can be found on the tool’s new website, DoulCi. Dutch publication De Telegraaf first reported news of the hack this morning.
Security researcher and iOS hacker Steven De Franco described the bypass as a “man-in-the-middle attack,” which means that it intercepts traffic going between a device and Apple’s servers. “It seems like it’s a firmware-related bug,” said De Franco in an interview with Cult of Mac. “So it would require a new update [from Apple] to patch it.”
When the hack is used and an iPhone is tricked past Activation Lock, the SIM card becomes unreadable “because they don’t have Apple’s private keys to tell the phone whether it’s unlocked or not,” explained De Franco. The two hackers behind DoulCi have sai they have a fix coming for the SIM block issue.
@AquaXetine thank’s team… More power…… from PH… pic.twitter.com/XR2Mb1OD4B — catac (@c4tac) May 21, 2014
The DoulCi website says the tool was “built with love for the people to give them a second chance to get there iDevices working again” and is “only for personal use.”
Tweets show that thousands of locked iPhones around the world have been bypassed using the tool just today. Most of the tweets thanking the two hackers come from outside of the U.S, where stolen iOS devices are shipped and sold at a premium on the black market.
In the Philippines, a Twitter user showed six iPhones that were unlocked.
@AquaXetine @MerrukTechnolog tnx for this,,,,more love from the philippines……LONG LIVE doulCi!!!!! pic.twitter.com/ZgTxaa0tTT
— esonglance (@esonglance) May 21, 2014
Another satisfied unlocker in Asia tweeted the following:
Twitter / abraham91612877: @AquaXetine pic.twitter.com/LkhcVlgscq https://t.co/sx2k4HssZz — Mscv50 (@Mscv50) May 21, 2014
The hackers claim the project has been a huge success. Earlier today, they posted screenshots of server logs claiming 5,700 devices had been unlocked in just five minutes. Later, they claimed another 10,000 devices had been unlocked. The two hackers say they worked on the exploit for five months and contacted Apple in March. Apple did not respond to Cult of Mac’s requests for comment.
More then 5700 devices was processed today by #doulCi server in 5 minutes see you next time with love of #doulCiTeam pic.twitter.com/vJCLlnX0Kg — Maroc-OS (@MerrukTechnolog) May 21, 2014


