Apple’s Gatekeeper feature was designed to keep even the most advanced users from accidentally installing malicious software on their computers, but a super-simple exploit lets hackers sneak malware onto your Mac.
The exploit was discovered by Patrick Wardle, director of research at security firm Synack. Wardle found that the exploit is made possible thanks to a key design shortcoming in Gatekeeper that lets an attacker use a binary file already trusted by Apple to execute malicious files.
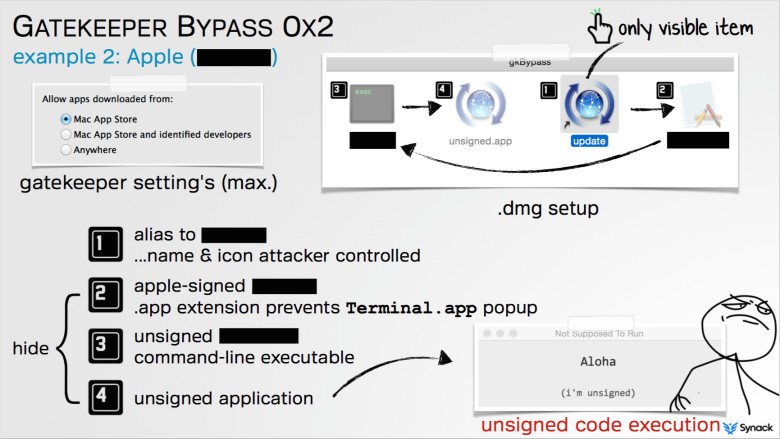
Here’s how it works:
Gatekeeper is designed to check digital certificates of downloaded apps before they’re installed to ensure they are signed by an Apple developer or came from the Mac App Store. The problem is that, even if Gatekeeper is set to its highest setting, the exploit still makes it past OS X’s digital bouncer with the trusted binary file, and can then execute other malicious programs attached with the rest of the installation.
“If the application is valid — so it was signed by a developer ID or was (downloaded) from the Mac App Store — Gatekeeper basically says ‘OK, I’m going to let this run,’ and then Gatekeeper essentially exits,” Wardle told Ars Technica. “It doesn’t monitor what that application is doing. If that application turns around and either loads or executes other content from the same directory… Gatekeeper does not examine those files.”
Once the exploit is complete, an attacker could install trojans or other malicious apps to glean a victim’s banking info, steal passwords or record audio and video without users’ knowledge.
Wardle says he notified Apple of the exploit 60 days ago and plans to present his findings at the Virus Bulletin International Conference on Thursday in Prague. The good news is Apple is aware of the flaw and is working on a patch to fix the underlying cause. The bad news is Wardle might not be the only one to have noticed the simple exploit.
“If I can find it, you have to assume groups of hackers or more sophisticated nation states have found similar weaknesses,” he said.
Source: Ars Technica