Apple has released security patches to fix the Heartbleed bug on AirPort base stations, and SSL-based security updates for Apple TVs and Macs.
You should probably go and update all of them as soon as possible.
Don’t panic though. The vulnerability only kicks in if you have Back to My Mac enabled on your new AirPort base station:
Impact: An attacker in a privileged network position may obtain memory contents
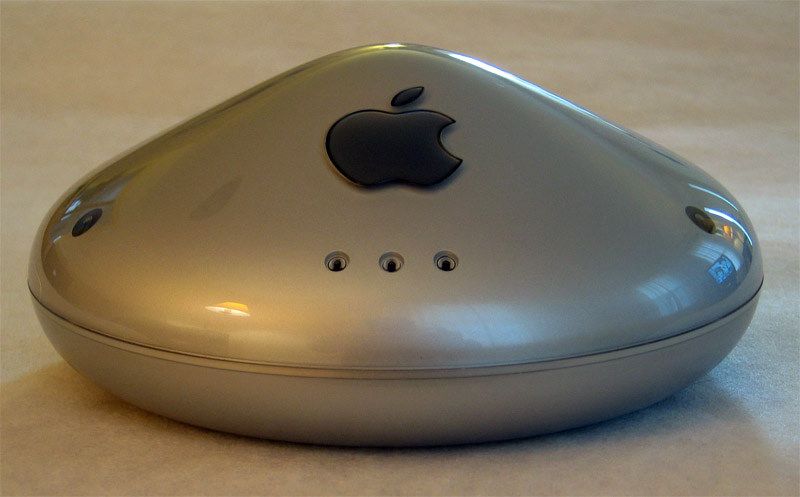
Description: An out-of-bounds read issue existed in the OpenSSL library when handling TLS heartbeat extension packets. An attacker in a privileged network position could obtain information from process memory. This issue was addressed through additional bounds checking. Only AirPort Extreme and AirPort Time Capsule base stations with 802.11ac are affected, and only if they have Back to My Mac or Send Diagnostics enabled. Other AirPort base stations are not impacted by this issue. [Emphasis added]
The Apple TV and Mac updates all feature a fix for what’s called a “triple-handshake” attack. This isn’t a neat StreetFighter II special move, although it obviously should be. Instead, it’s this:
Impact: An attacker with a privileged network position may capture data or change the operations performed in sessions protected by SSL
Description: In a ‘triple handshake’ attack, it was possible for an attacker to establish two connections which had the same encryption keys and handshake, insert the attacker’s data in one connection, and renegotiate so that the connections may be forwarded to each other. To prevent attacks based on this scenario, Secure Transport was changed so that, by default, a renegotiation must present the same server certificate as was presented in the original connection.
I’ll be hitting the mailing list of close friends who I warn when something like this comes up, and trying to coordinate my own updates so I don’t have to spend too long without an Internet connection.
Source: Apple