This Apple Enterprise Management post is presented by Jamf.
Even before the COVID-19 pandemic changed how employers and employees operate, remote work had become increasingly prevalent. By 2016, 43% of the U.S. workforce worked from home at least to some extent, according to Gallup. The pandemic added millions more and might tilt the balance toward remote work permanently.
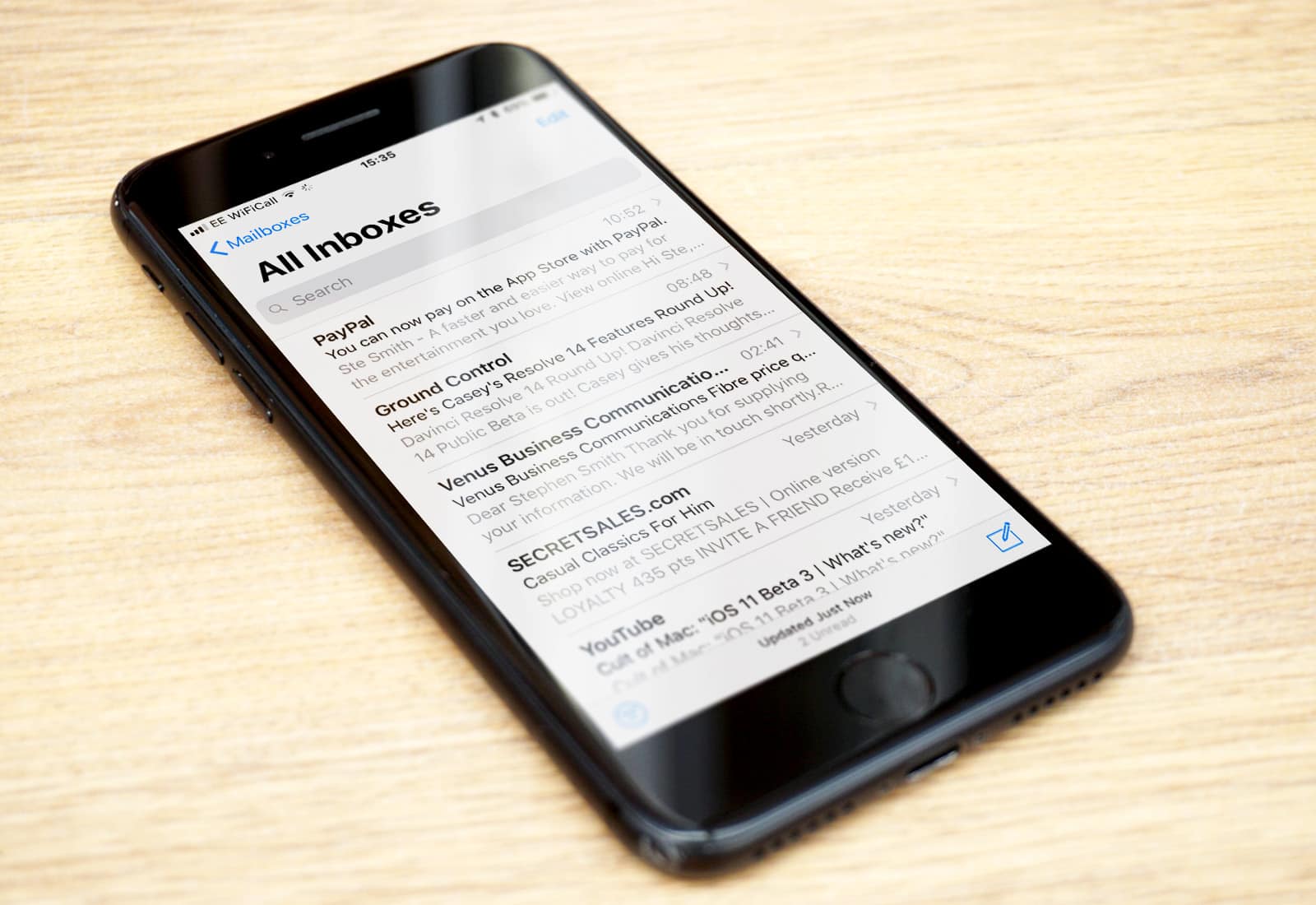
So, now more than ever, organizations large and small must figure out how to manage, connect and secure all devices their staff members use, in workplaces and remotely. For enterprises that prefer to have iPhones, Macs and iPads in the mix, effective Apple Enterprise Management is crucial.










![Using Zoom? Take these steps to protect your privacy [Updated] yoga class zoom](https://www.cultofmac.com/wp-content/uploads/2020/03/anupam-mahapatra-Vz0RbclzG_w-unsplash.b0526f88e2f547429ee8634ed807108a.jpg)