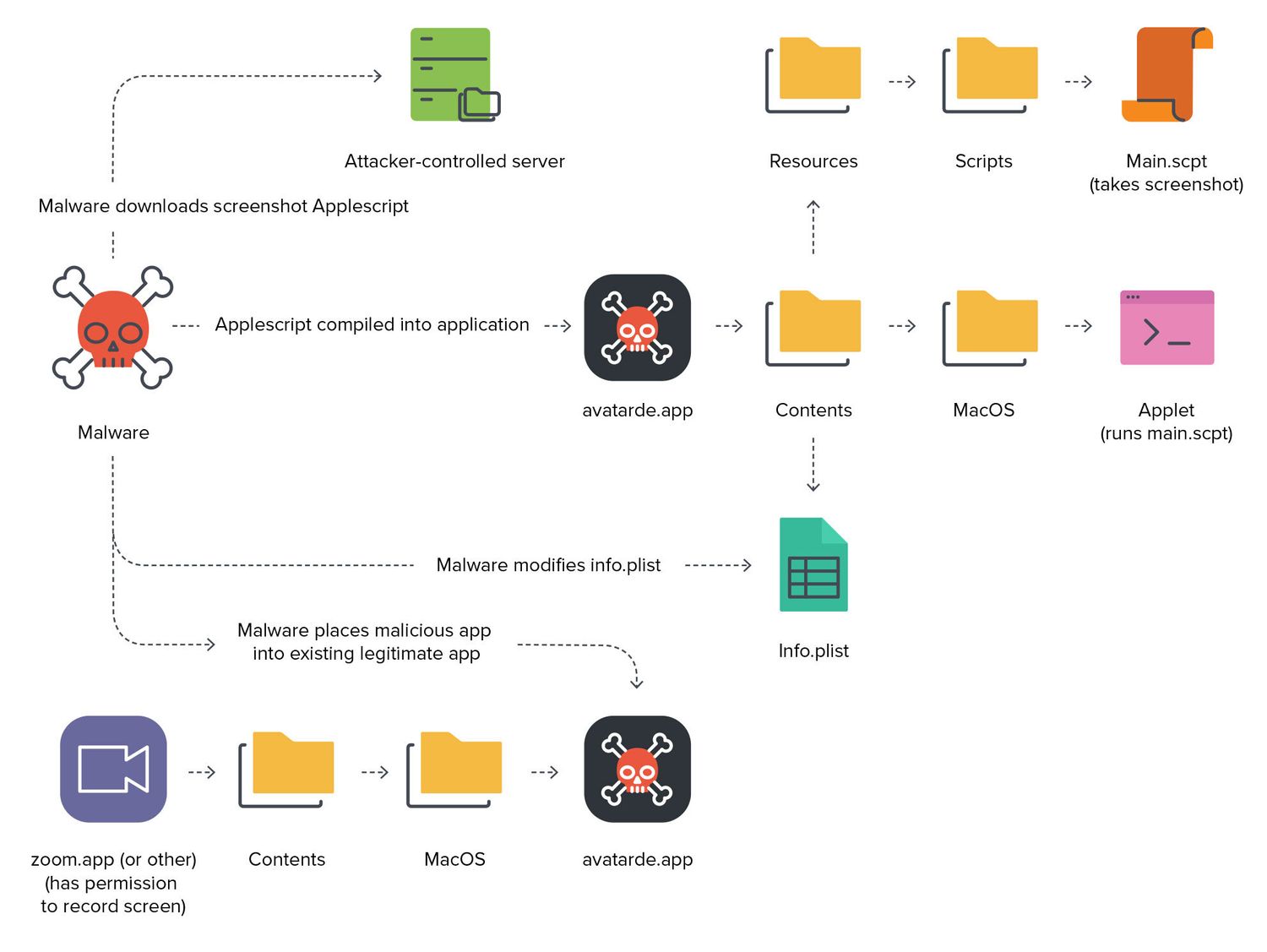
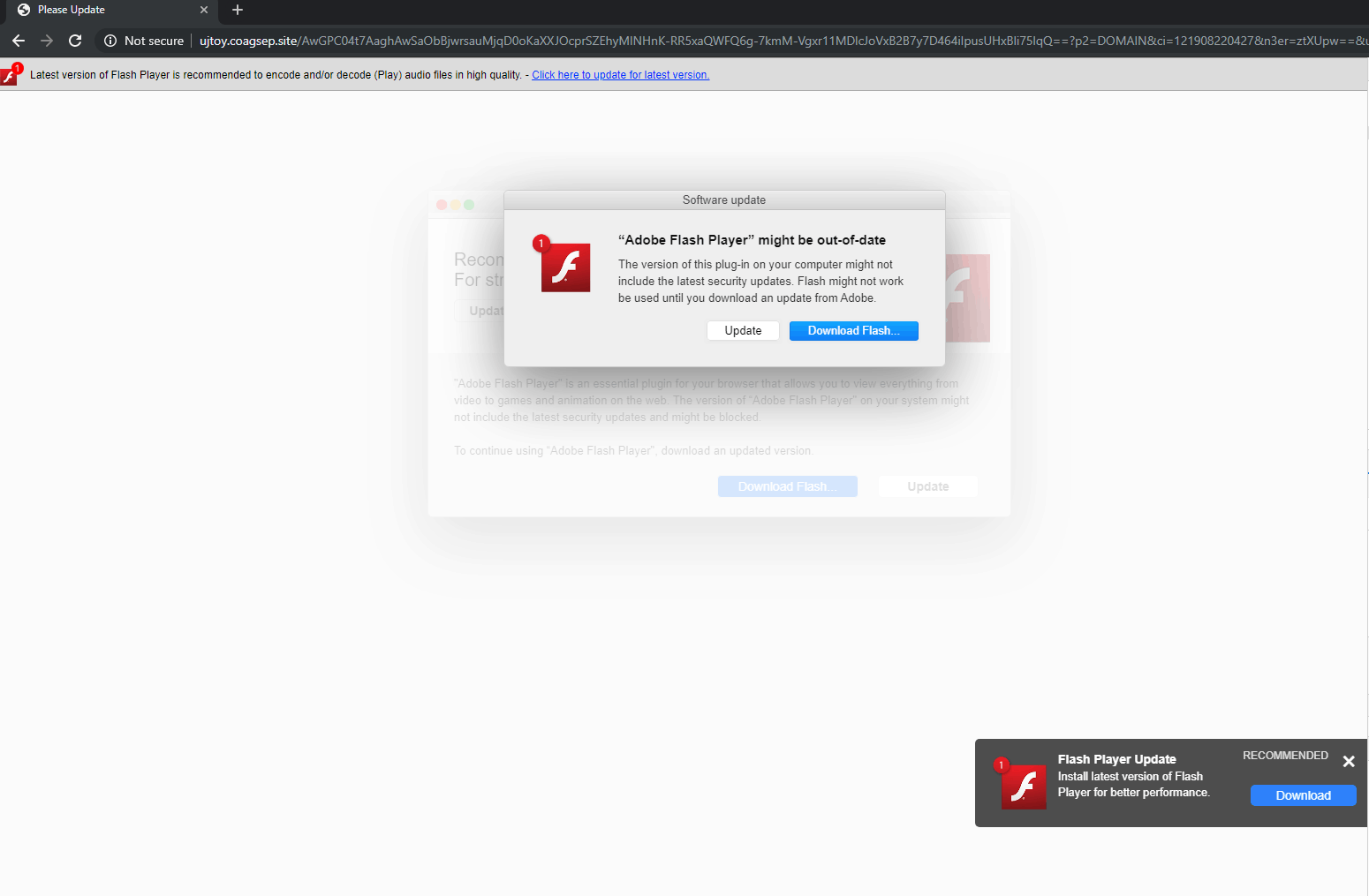
Security researchers have found a serious exploit in all Apple M-series processors. The hard-wired flaw could potentially could be used by hackers to get user credit card information or read encrypted messages.
The flaw exposes precious encryption keys, and it’s baked into the hardware — so it can’t easily be patched without a performance penalty. Here’s what you need to know.


![First-ever iOS trojan steals your face to break your bank [Updated] Trojan horse: first ios trojan goldpickaxe](https://www.cultofmac.com/wp-content/uploads/2024/02/pexels-kemal-hayit-6474435.jpg)