Back in August, we told you about a serious SMS security flaw with the iPhone that opened the door to text message spoofing. At the time, Apple told users they could protect themselves by using its iMessage service rather that traditional SMS messages, but the Cupertino company appears to have rectified the issue in iOS 6.
The problem was first discovered by iOS hacker Pod2g, who warned that it could be used by malicious attackers to steal your personal data. It’s all to do with the way in which the iPhone handles text messages. Pod2g explained:
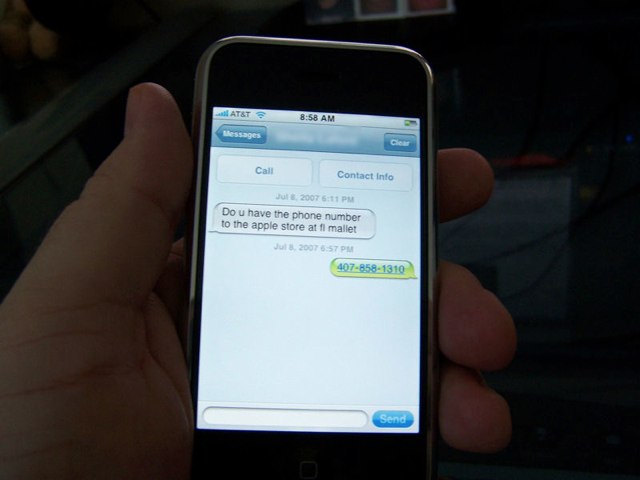
A SMS text is basically a few bytes of data exchanged between two mobile phones, with the carrier transporting the information. When the user writes a message, it is converted to PDU (Protocol Description Unit) by the mobile and passed to the baseband for delivery.
[…] In the text payload, a section called UDH (User Data Header) is optional but defines lot of advanced features not all mobiles are compatible with. One of these options enables the user to change the reply address of the text. If the destination mobile is compatible with it, and if the receiver tries to answer to the text, he will not respond to the original number, but to the specified one.
Most carriers don’t check this part of the message, which means one can write whatever he wants in this section : a special number like 911, or the number of somebody else.
Attackers could have taken advantage of the flaw by sending you a text message that, for example, appeared to be from your bank requesting certain information, but actually sent your response directly to them.
But according to jailbreaker Joshua Hill (aka p0sixninja), the iOS 6 update that Apple released to the public on Wednesday includes an “insane number of security fixes,” one of which closes the SMS flaw.
That means you can go back to texting friends who don’t have iMessage again.
Source: Joshua Hill
Via: The Verge