Now that Apple is fixing the in-app purchasing exploit that Russian hacker Alexei Borodin brought to light this week, it seems as if he’s at it again. This time, however, it’s an in-app purchasing hack that works in the Mac App Store.
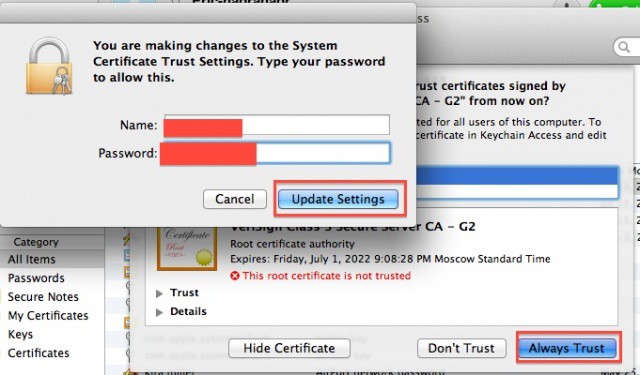
The method here is similar as the one Borodin used in iOS, with the user installing some fake security certificates and then pointing the Mac’s DNS servers at a false server run by Borodin. The remote server then pretends to be the actual Mac Store and verifies the purchase, bypassing the real system for in-app purchases set up by Apple and use by developers of Mac apps. Borodin claims that this system has allowed approximately 8.4 million free purchases so far.
This is another blow to Apple, who earlier today announced that iOS developers can utilize a temporary fix for their iOS 5 apps to prevent the iOS hack from working and stealing their in-app purchases, with a more permanent fix set for iOS 6, coming soon. We can only assume that Apple will create a similar fix for the Mec OS X exploit, possibly even fold it into the upcoming OS X release of Mountain Lion (10.8).
Granted, iOS apps tend to rely on in-app purchases more than OS X apps do, but stealing them is theft, even on a smaller scale. It can only hurt Apple to let such an exploit exist any longer than is strictly necessary to create a solid fix.
Why Borodin is doing this is unclear – does he enjoy the technical challenge, the game with Apple, or is he protesting the system of in-app purchasing itself? We can only advise at this point that we all stay clear of such an exploit, as it not only deprives Apple of revenue, but developers as well, none of whom have the cash reserves Apple does.
Source: The Next Web