One of the mobile news items this week was the discovery by developer Gareth Wright of a vulnerability in the Facebook apps for both iOS and Android. At issue in the iOS version of the Facebook app is the fact that a user’s login data is stored in a clear text .plist file. Copying that file to another device will allow full access to a person’s Facebook account.
Facebook was quick to point out that this file could only be copied directly from an iOS device if the device had previously been jailbroken. Wright responded by saying that the portion of the iOS file system where the data is located can be accessed by connecting any iOS device (jailbroken or not) to a Mac or PC running iTunes and creating a backup. With the right tools, its fairly easy to search an iOS device backup or even the filesystem on a connected device.
This brings up an important issue for businesses deploying iOS devices or operating a BYOD program – iOS backups made through iTunes can be an attack vector to retrieve business data.
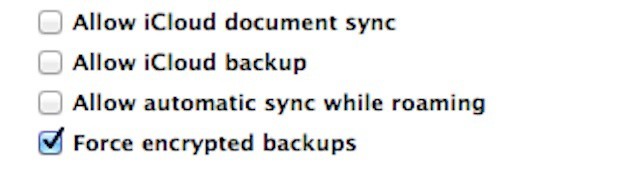
While this is an issue, it’s also one that’s relatively easy to solve. iTunes offers the ability to encrypt iOS backups. While an acceptable use policy is one way to promote encrypted backups, the best way to ensure that employees choose to use encrypted backups is to not offer a choice. You can use a device management solution to force an iOS device to create encrypted backups. The option can be used as part of a larger device management strategy that includes a fully featured MDM suite. Even without full scale device management, this requirement can be put in place using a simple configuration profile created with Apple Configurator of the iPhone Configuration Utility for Macs and Windows PCs.