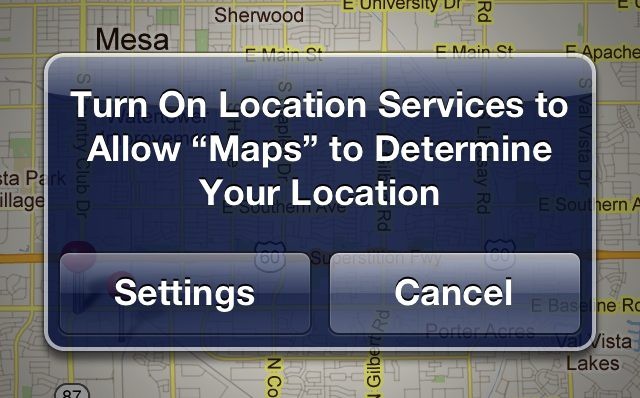
Over the last few weeks, third-party iOS developers received a lot of heavy venom from the Internet after reports surfaced that apps are accessing users’ address book information without users’ permission. It appears that the situation is worse than first thought and that apps can access more than just address books without notifying users. Photos on iOS devices are also susceptible to apps once a user has granted an app permission to their location information.
Once a user okays an app to view their location information, that app has the ability to view and copy the user’s entire photo library without providing any warning or notification to the user.
“Conceivably, an app with access to location data could put together a history of where the user has been based on photo location,” said David E. Chen, co-founder of Curio, a company that develops iOS apps. “The location history, as well as your photos and videos, could be uploaded to a server. Once the data is off of the iOS device, Apple has virtually no ability to monitor or limit its use.”
All photos taken by an iPhone carry geotag information, which is advantageous to apps like iPhoto that can organize photos based on location once they’ve been imported into the user’s library. It’s odd that Apple is tying location-data access with full access to the photo library rather than only permitting apps to read the geotag information.
This information has been known to developers for quite sometime, but the New York Times points out that Apple hasn’t done much to fix the problem and that if a malicious app sneaks by Apple’s approval processes there could be some disastrous results. Apple’s walled garden approach seems like a great solution for problems like these, except apps that provide different functionality than advertised sneak through all the time. Countless tethering apps have snuck through Apple’s review panel, and even Camera+ hid volume shutter-button functionality in their app before Apple included it in iOS 5. Most of these apps only get banned once Apple has been alerted through the press.
The New York Times even went so far as hiring an app developer to build a simple “PhotoSpy” app that pulled information from an iPhone. Once the PhotoSpy app was started, it asked for access to location data. Once it was given access to location data, it began to siphon photos to a remote server. As soon as the photos had been uploaded to a remote server they are no longer under the users control. The PhotoSpy app was never submitted to the App Store, but what’s to stop someone else from doing it?
What we take away from all these privacy scandals is that users should never be certain that their information is 100% safe. If you got nudie photos of Scarlett Johansson that you don’t want the web to see, then it’d probably be a good idea to keep those off your iPhone, lest some malicious app steal them away to TMZ for a fat stack of cash.
[via NYT]