Apple computers have a unique boot option called Target Disk Mode which allows access to a system’s hard drives via Firewire cable in older Macs and a Thunderbolt cable in newer models. You access Target Disk Mode by pressing and holding the “T” key while the system starts and until you see either the Firewire or Thunderbolt symbol on the screen.
Once you see the symbol appear you can connect your computer to another Mac Or PC and the hard drives on the Mac in Target Disk Mode will mount on the other system with full access. Since you have full access to the startup disk your data’s security is compromised, but here are a few ways to fix that. I’ll show you how in today’s tip.
File Vault, File Vault 2 or Third-Party Encryption
The easiest way to protect your data from prying eyes is to use File Vault. File Vault is available on all Macs, but only Macs running Mac OS X Lion have File Vault 2 which includes full disk encryption. Macs running Mac OS X Snow Leopard’s version of File Vault only protects the user’s Home folder and there are third-party apps like Exces or PGP that you can use as encryption options on your Mac (virtual drives, full disk encryption, etc.).
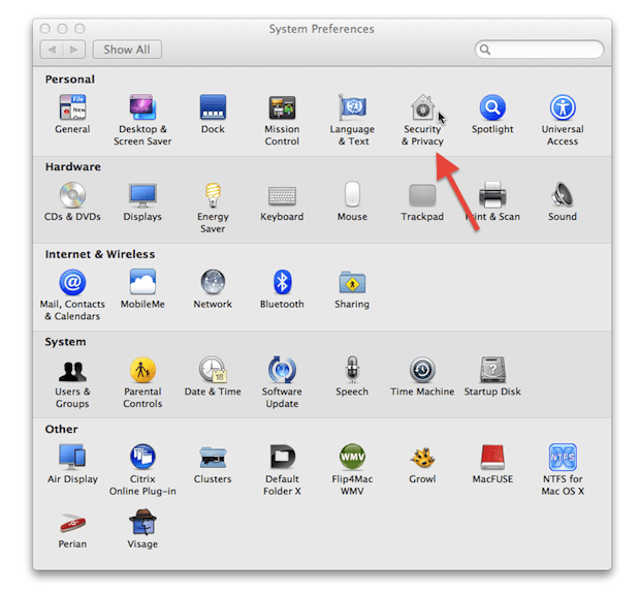
You activate File Vault 2 via the Security & Privacy preferences panel inside of System Preferences. I’ve got a how to about using File Vault 2 on systems running Mac OS X Lion that will show you how to fully encrypt your startup disk. So why would you do this? The reason is that even in Target Disk Mode the encrypted disk isn’t accessible unless you have a password. Bonus: You can go a step further using this other how to I wrote using File Vault 2 to encrypt external drives.
Firmware Password
Simply enabling a firmware password would prevent access to your Macs startup disk because unless you know that password your Mac will not even boot into Target Disk Mode. Mac OS X Lion’s new Recovery HD partition has the utility needed to set the firmware password. Just restart your Mac while pressing and holding the Command+R keys and your Mac will boot into the recovery partition. You’ll find the Password Utility on the Utilities menu once you see the recovery partitions menu.
A lengthy explanation about enabling a firmware password is found in this Apple Knowledge Base document https://support.apple.com/kb/HT1352. People using Macs that don’t support the recovery partition or Macs running Mac OS X Snow Leopard should read HT1352.
It is important to note that in some cases if you loose your firmware password you may have to visit an Apple authorized service center to get it reset. So make sure that you keep a record of it.
Restrict Physical Access
Since the firmware password isn’t 100% foolproof because hardware changes can cause your Mac to bypass the firmware password. This means you might not need that service center visit after all, but it also means that firmware passwords aren’t all that great either. Physical access restrictions are the best way to protect your Mac since if, for example, you lock a MacBook Air in a drawer not even you will be able to use it, but your data is safe from everyone including you!
Conclusion
In summary you have three options to protect your data from being accessed via Target Disk Mode listed in the order of the most effectiveness: restrict physical access to your Mac, File Vault encryption and a firmware password. The first option will be the best since no one can get to your Mac while the second is best when used in combination with the latter. The firmware password will act as a deterrent for less experienced hackers or thieves, but since it can be by-passed encryption is what saves the day in the end. If you use File Vault and a firmware password you’ll be able to access your data in the best possible way with the fewest hassles.
![Protect Your Data From Target Disk Mode Security Risks [OS X Tips] targetdisktb](https://www.cultofmac.com/wp-content/uploads/2011/09/targetdisktb.jpg)